Data logging by essential IT equipment has been around since the beginning of the modern computer era. Operating systems, application software, hardware, and a plethora of IT equipment in and on the network generate log files, and IT professionals can often find themselves knee deep in an overwhelming amount of data, especially as cloud services are added to the mix. But, the truth is that if used properly, log data can be a very good friend to both IT and business operations. So let’s look at the top reasons to love your log data.

1. It is invaluable information for problem solving
Yes, there are no ends to system status messages telling you that everything is OK, but that’s why information related to issues really stands out. Be that log events pointing to physical issues with hardware, configuration issues with software, or process automation issues with development or business applications, logs contain the keys to quickly finding and solving problems that directly impact your business workflow and operations. So while analyzing log data can keep you abreast of the status of your current operations, it is invaluable when problem solving and keeping those operations running optimally.
2. There’s no better way to find comparative data over time
Analyzing log data when looking to solve system behavior issues requires being able to look at the systems that you are inspecting over extended time frames. Log data is easy to store, and maintaining information that goes back years is rarely an issue. Using the right tools allows you to mine that data for the key nuggets that allow both problem solving and system optimization. Sporadic issues that cause service problems are the bane of IT; using log data over extended time periods is often the only way to properly analyze and solve these types of problems. Discovering obscure conditions that cause problems is often only possible through the analysis of log data.
3. Maintaining security across the enterprise
With so many avenues of attack into a modern enterprise, collating data across multiple applications and services to find patterns of attempts to circumvent security processes, from threats both external and internal is another area where analyzing log data can really shine. As Ian Fleming‘s character Auric Goldfinger say, “Once is happenstance; twice is coincidence. Three times is enemy action.” Log analysis tools can scan log data across the enterprise to alert IT to those less than accidental attempts to negate established security policies and procedures. Not all attacks are obvious nor attempt to overwhelm security. Being able to find the subtlest attempts to breach security requires the ability to look at log data from many sources.
4. Logs are for business analytics, too
Today so much business is done via outward-facing websites and cloud-based services, and it is important to be able to analyze the usage patterns of applications and services, along with data such as average response time and workload to get a complete picture of the how your system is being used from a business perspective. With many different applications and services coming together to produce the business-focused product, using log data from this multitude of sources becomes one of the best ways for business analysts to determine how business services are utilized and what can be done to improve the customer experience.
While many applications offer their own interfaces into what their products are doing and may extend that to allow the IT guy to see how their product is interacting with other services, few, if any offer any significant level of detail across a heterogeneous business environment. But almost every a hardware device, application, and service offers the ability to generate log data that reports on its operation. And, making the most from that data will make for a more competitive and agile business.
Article Tags
Related blog posts
Products and Tools
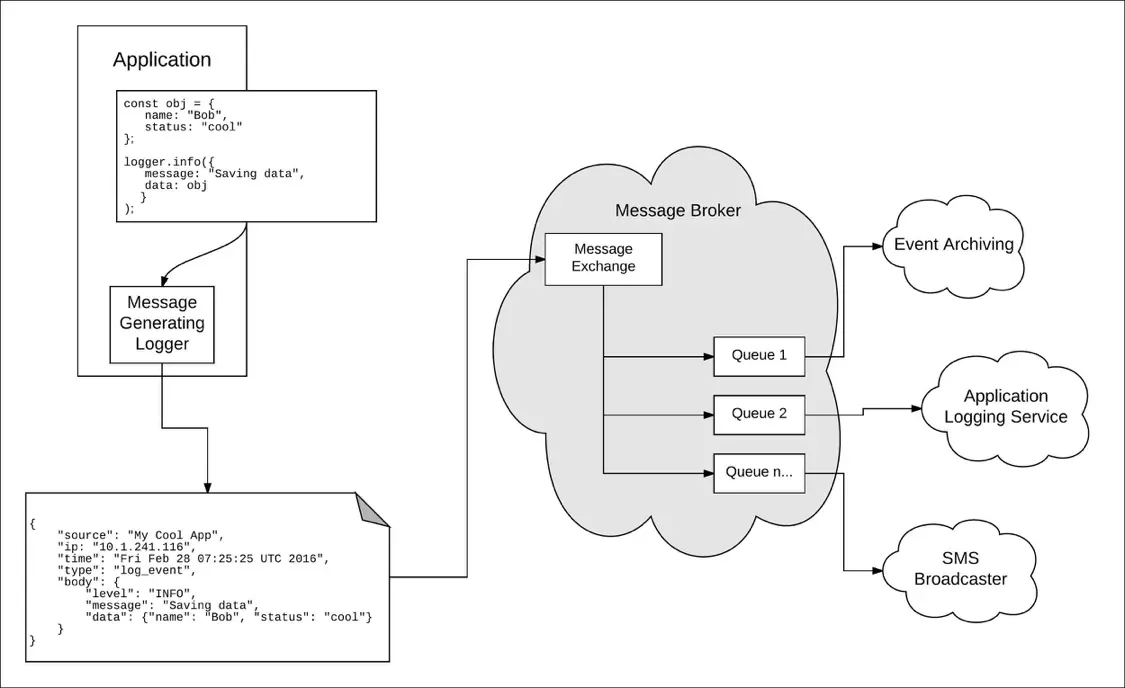
Taking a Message-Based Approach to Logging
Robert Reselman
Detection and Response
6 Best Practices for Effective IT Troubleshooting
Robert Reselman

Security Operations
3 Steps to Building an Effective Log Management Policy
Robert Reselman

Security Operations
3 Core Responsibilities for the Modern IT Operations Manager
Robert Reselman
