If you're in security, you've likely already heard about the ShellShock vulnerability (aka Bash Bug, CVE-2014-6271, and CVE-204-7169). We have reviewed how ShellShock is being exploited, and the disclosed vectors are not applicable to our UserInsight deployment, yet we're following the security community's lead around patching all of our systems.
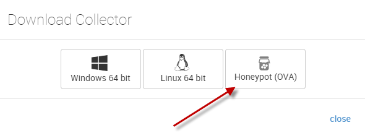
- Detect port scanning through production honeypots: After getting the first foothold on the network, attackers need to get the lay of the land to know what to attack next. UserInsight detects port scanning through honeypots on your network. If you are a UserInsight subscriber and you haven't deployed any honeypots so far, simply click on the Collectors menu, the Download Collectors button, and download the Honeypot OVA. Once you've started the OVA as a virtual machine and hooked it up to UserInsight, it will alert you on any portscanning activity in the subnet. Learn more about honeypots and honeyusers in UserInsight.
- Detect lateral movement through agentless endpoint visibility: Surveys show that attackers love stealing passwords and passing off credentials to move through the network. When they use domain credentials, you may see this on Domain Controller logs. However, we learned from our internal penetration testing team that they mostly use pass-the-hash using local credentials to move from endpoint to endpoint, never triggering activity on the domain controller. This type of movement can only be detected by monitoring the endpoints, which can typically only be achieved by deploying and managing an endpoint agent. UserInsight provides this endpoint visibility without an endpoint agent by leveraging the proven Nexpose scanning technology to gather Windows logs from the endpoints for analysis. That way, you're fully covered for abuse of domain and local credentials without having to deploy and manage an endpoint agent.
If you're a UserInsight subscriber and have questions about ShellShock or these detection mechanisms, please contact your Rapid7 account manager.
More information
If you want to know more information about bashbug and how you can use Rapid7 products to detect it, we've gathered all information we've published about BashBug right here: bashbug CVE-2014-6271 (shellshock): What is it? How to Remediate | Rapid7
Related blog posts

Vulnerabilities and Exploits
CVE-2026-0826: How an Old Bug Can Feed AI-Powered Impersonation
Douglas McKee, Director, Vulnerability Intelligence

Vulnerabilities and Exploits
CVE-2026-0826: Critical unauthenticated stack buffer overflow in HP Poly VVX and Trio VoIP Phones (FIXED)
Stephen Fewer

Vulnerabilities and Exploits
Authenticated RCE via Argument Injection in Gogs (NOT FIXED)
Jonah Burgess

Vulnerabilities and Exploits
CVE-2026-20182: Critical authentication bypass in Cisco Catalyst SD-WAN Controller (FIXED)
Jonah Burgess, Stephen Fewer