Rapid7, Inc. (Rapid7) discovered vulnerabilities in Aladdin Connect retrofit kit garage door opener and Android mobile application produced by Genie. The affected products are:
- Aladdin Garage door smart retrofit kit, Model ALDCM
- Android Mobile application ALADDIN Connect, Version 5.65 Build 2075
Rapid7 initially reported these issues to Overhead Door — the parent company of The Genie Company — on August 22nd 2023. Since then, members of our research team have worked alongside the vendor to discuss the impact, resolution, and a coordinated response for these vulnerabilities.
Product description
The Aladdin Connect garage door opener (Retrofit-kit) is a smart IoT solution which allows standard electric garage doors to be upgraded to support smart technology for remote access and use of mobile applications for opening and closing of the garage door.
Credit
The vulnerabilities in Genie Aladdin Connect retrofit garage door opener and mobile application were discovered by Deral Heiland, Principal IoT Researcher at Rapid7. They are being disclosed in accordance with Rapid7’s vulnerability disclosure policy after coordination with the vendor.
Vendor statement
Trusted for generations by millions of homeowners, The Genie Company is committed to security, and we collaborate with valued researchers, such as Rapid7, to respond to and resolve vulnerabilities on behalf of our customers.
Exploitation and remediation
This section details the potential for exploitation and our remediation guidance for the issues discovered and reported by Rapid7, so that defenders of this technology can gauge the impact of, and mitigations around, these issues appropriately.
Android Application Insecure Storage (CVE-2023-5879) - FIXED
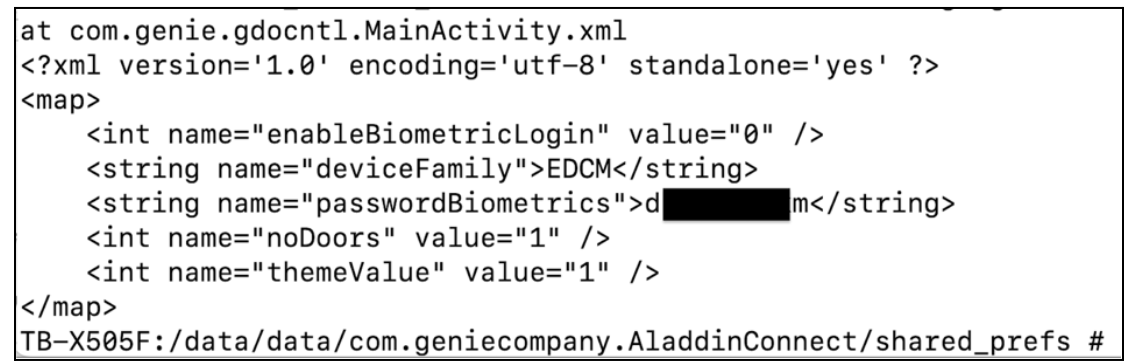
While examining the Android mobile application, Aladdin Connect, for general security issues, Rapid7 found that the user’s password was stored in clear text in the following file:
- /data/data/com.geniecompany.AladdinConnect/shared_prefs/com.genie.gdocntl.MainActivity.xml
The persistence of this data was tested by logging out and rebooting the device. Typically logging out and rebooting a mobile device leads to the data being purged from the device. In this case neither the file, nor its contents, were purged. Figure 2 is copy of file content after logout and reboot:
Exploitation
An attacker with physical access to the user’s smartphone (i.e., via a lost or stolen phone), would be able to potentially extract this critical data, allowing access to the user’s service account to control the garage door opener.
Remediation
To mitigate this vulnerability, users should set a password pin code on the mobile devices to restrict access.
Additional Note from Vendor
This vulnerability is tied to the biometric capability (touch or face recognition).
Mitigation: Update to the latest app upgrade available in the play store. App version v5.73
Cross-site Scripting (XSS) injected into Aladdin Connect garage door opener (Retrofit-Kit) configuration setup web server console via broadcast SSID name (CVE-2023-5880)
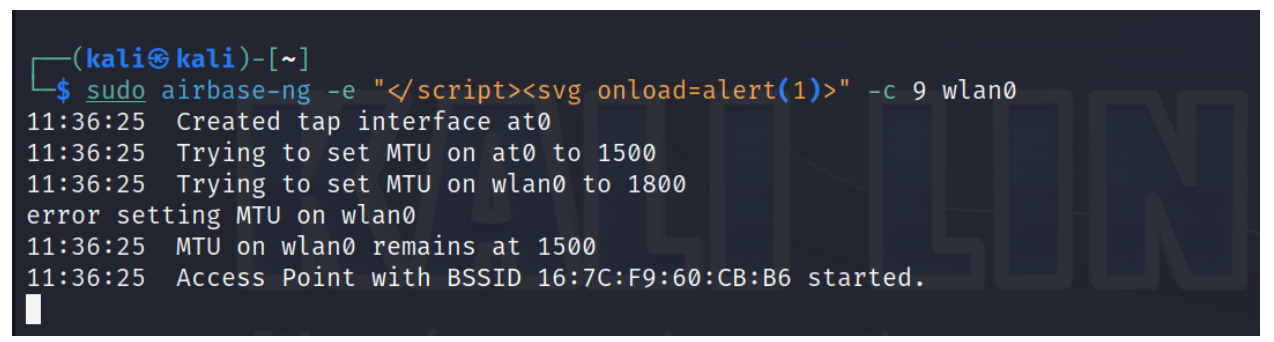
When the Aladdin connect device is placed into Wi-Fi configuration mode, the user web interface used for configuring the device is vulnerable to XSS injection via broadcast SSID names containing HTML and or JavaScript.
Exploitation
This XSS attack via SSID injection method can be done by running a software-based Wi-Fi access point to broadcast HTML or JavaScript as the SSID name such as:
- </script><svg onload=alert(1)>
An example of this is shown in Figure 3, using airbase-ng to broadcast the HTML and or JavaScript code:
In the example found in Figure 4, a simple alert box is triggered on the Aladdin base unit Wi-Fi configuration webpage from the above SSID name. Also, the image on the right of Figure 4 shows the actual web page source delivered to the end user. No user interaction is needed to trigger this, they only need to view the web page during configuration mode.
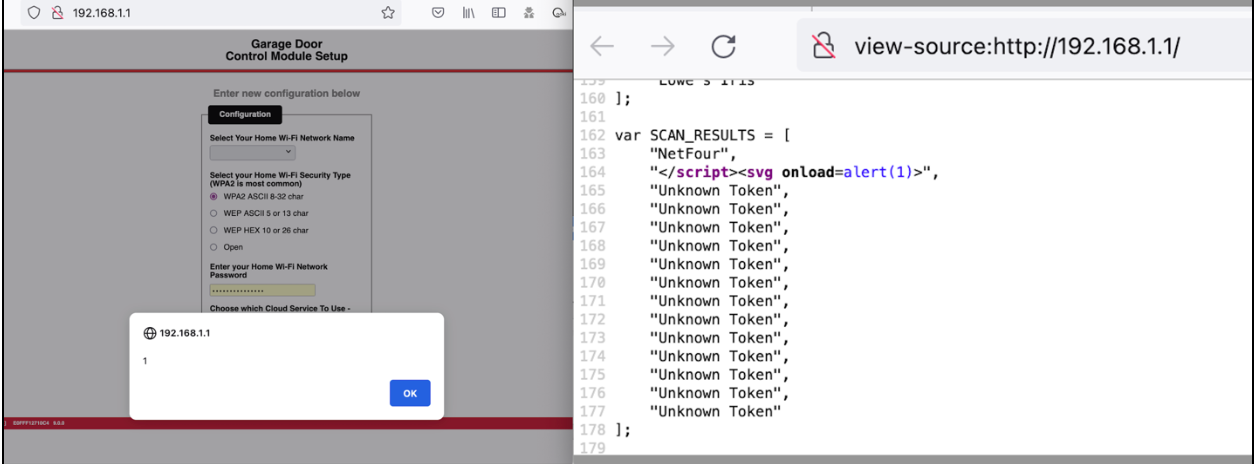
Also, a denial of service (DoS) of the Wi-Fi configuration page can be accomplished by just broadcasting an SSID containing </script> preventing the web page from being used to configure the device's setup. This corrupted web page is shown in Figure 5:
Remediation
To mitigate this vulnerability, users should avoid running setup if any oddly named SSIDs are being broadcast in the general vicinity, such as SSIDs containing HTML markup language and/or JavaScript code in their names.
Also, in general the mobile application can be used to set up and configure the Garage Door opener. This will avoid any direct interaction with the vulnerable “ Garage Door Control Setup” configuration page.
Additional Notes from the Vendor
This is a very low-impact vulnerability with minimal risk. This can only occur when the owner places the device in the wifi configuration mode for a limited period and the intruder operates within the 2.4 GHz band distance range during that limited configuration period. The device will not be impacted by the misconfiguration if that were to occur and it is fully capable of recovering from misconfiguration. The device cannot be operated with a misconfigured SSID as the device can only be claimed by the owner using the mobile app. There is no vulnerability in the mobile app which is the approved mode of device provisioning.
Mitigation: Use mobile app to configure the device.
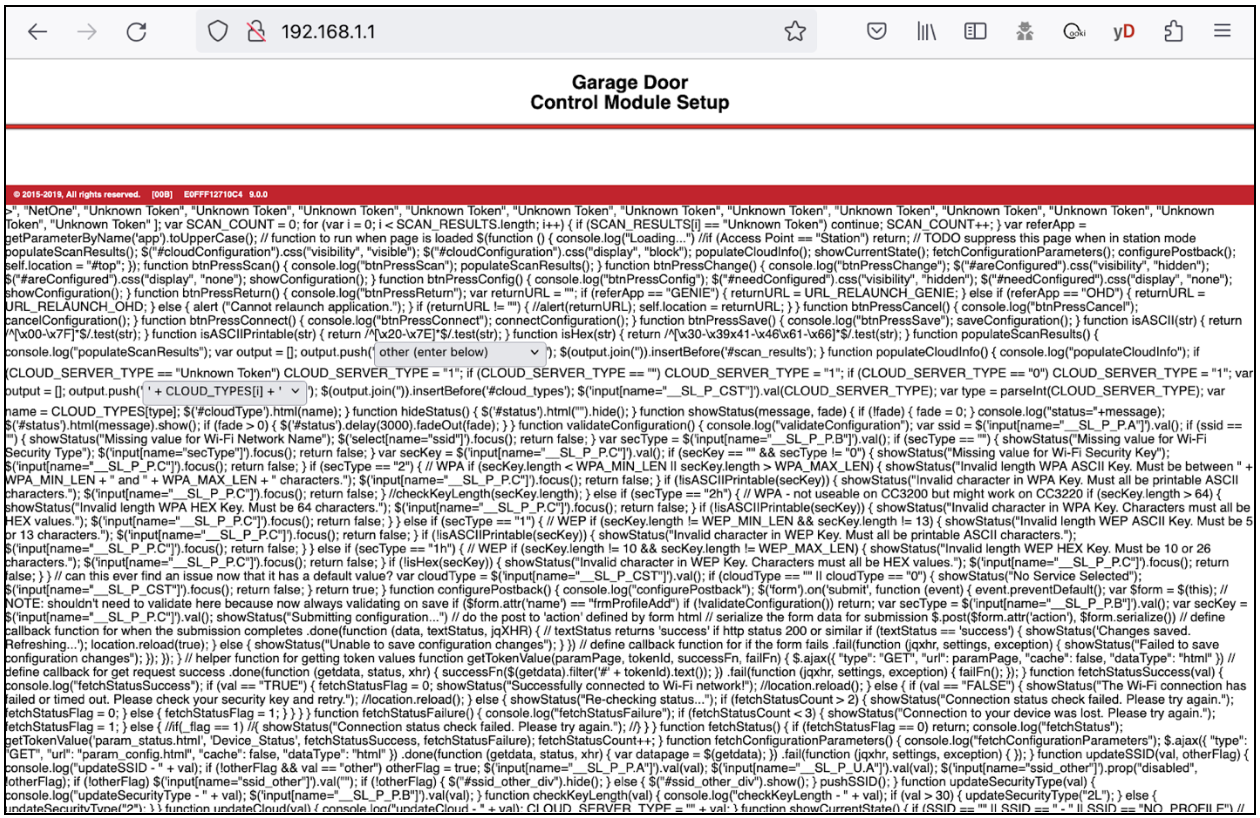
Unauthenticated access allowed to web interface for “Garage Door Control Module Setup” page (CVE-2023-5881) - FIXED
This vulnerability allows a user with network access to connect to the Aladdin Connect device web server's “Garage Door Control Module Setup” web page and alter the Garage doors connected WIFI SSID settings without authenticating.
Exploitation
The device allows unauthenticated access to Garage Door Control Module Setup configuration page on TCP Port 80, This allows anyone with network access to reconfigure the Wi-Fi settings without being challenged to authenticate. A sample of this access to the configuration web page is shown in Figure 6:
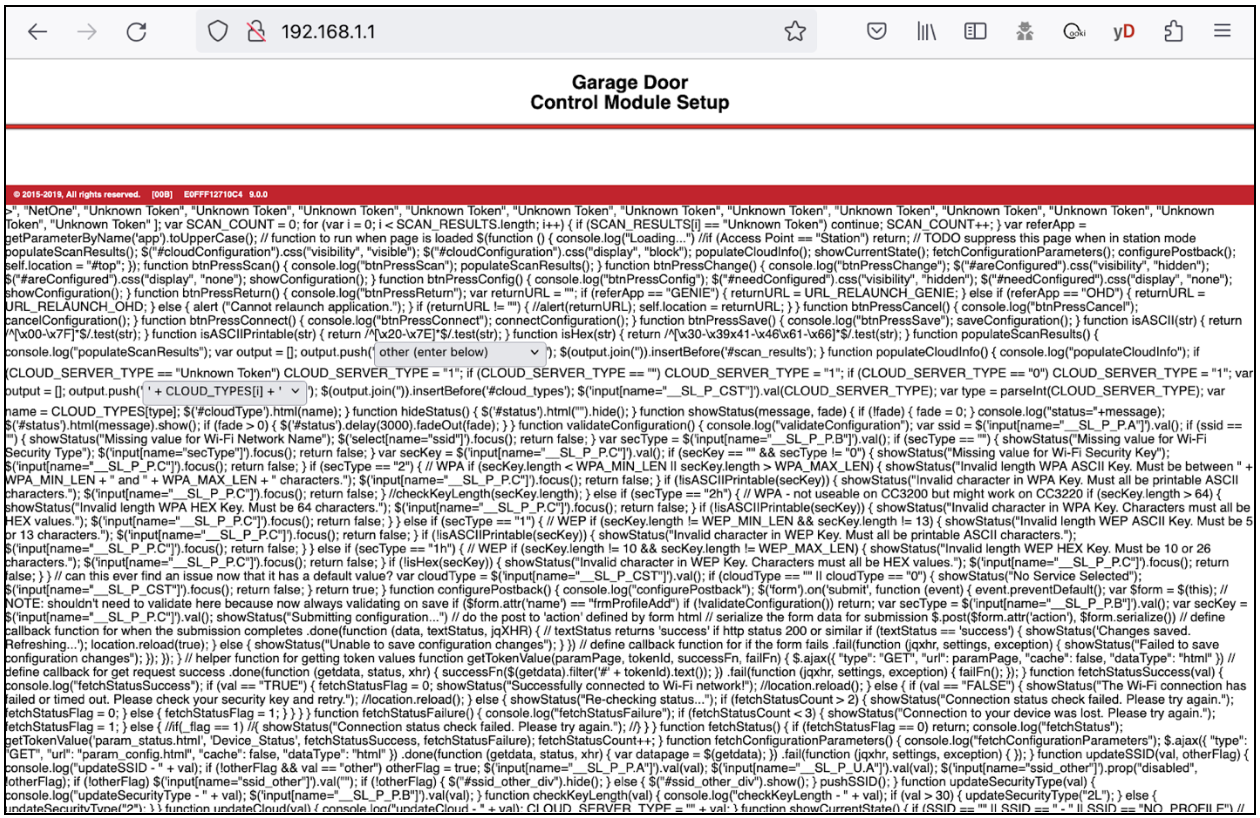
Remediation
To prevent exploitation, users should only attach the Aladdin Garage door smart retrofit kit to a network they own and control. Also, access to this network should not be allowed from any other network source such as the Internet.
Additional Notes from the Vendor
This is a very low-impact vulnerability with minimal risk. This can only occur when the intruder has access to the same local network as the retrofit kit (use the same network router), so the attack vector is limited to local. This web interface is not accessible from the internet. The device cannot be operated with a misconfigured SSID, as the device can only be claimed using the mobile app that an owner would use.
Mitigation: Update the Retrofit device to the latest software version, 14.1.1. Fix was automatically updated on all online devices as of December 2023. Please reach out to customer service to confirm if your device has the update.
Authenticated user access to others users data via service API - FIXED
An authenticated user can gain unauthorized access to other users’ data by querying the following API using a different device ID than their own.
- https://pxdqkls7aj.execute-api.us-east-1.amazonaws.com/Android/devices/879267
Here are sample fields that are potentially viewable data using this method:
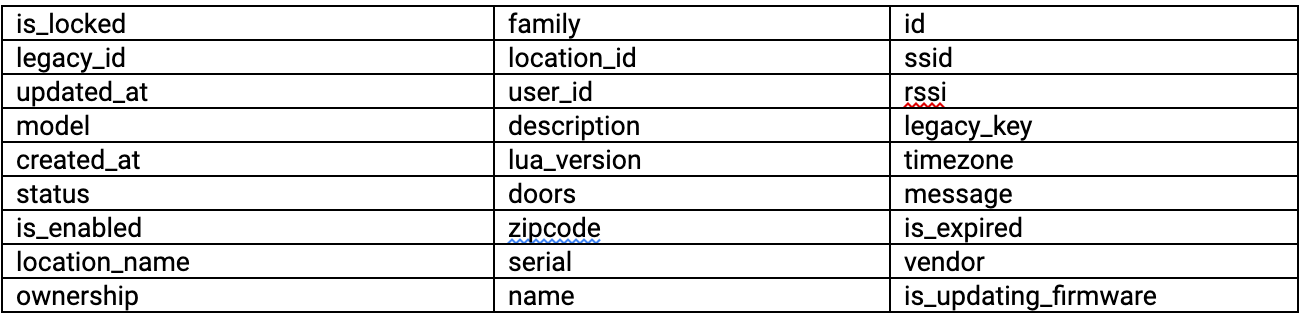
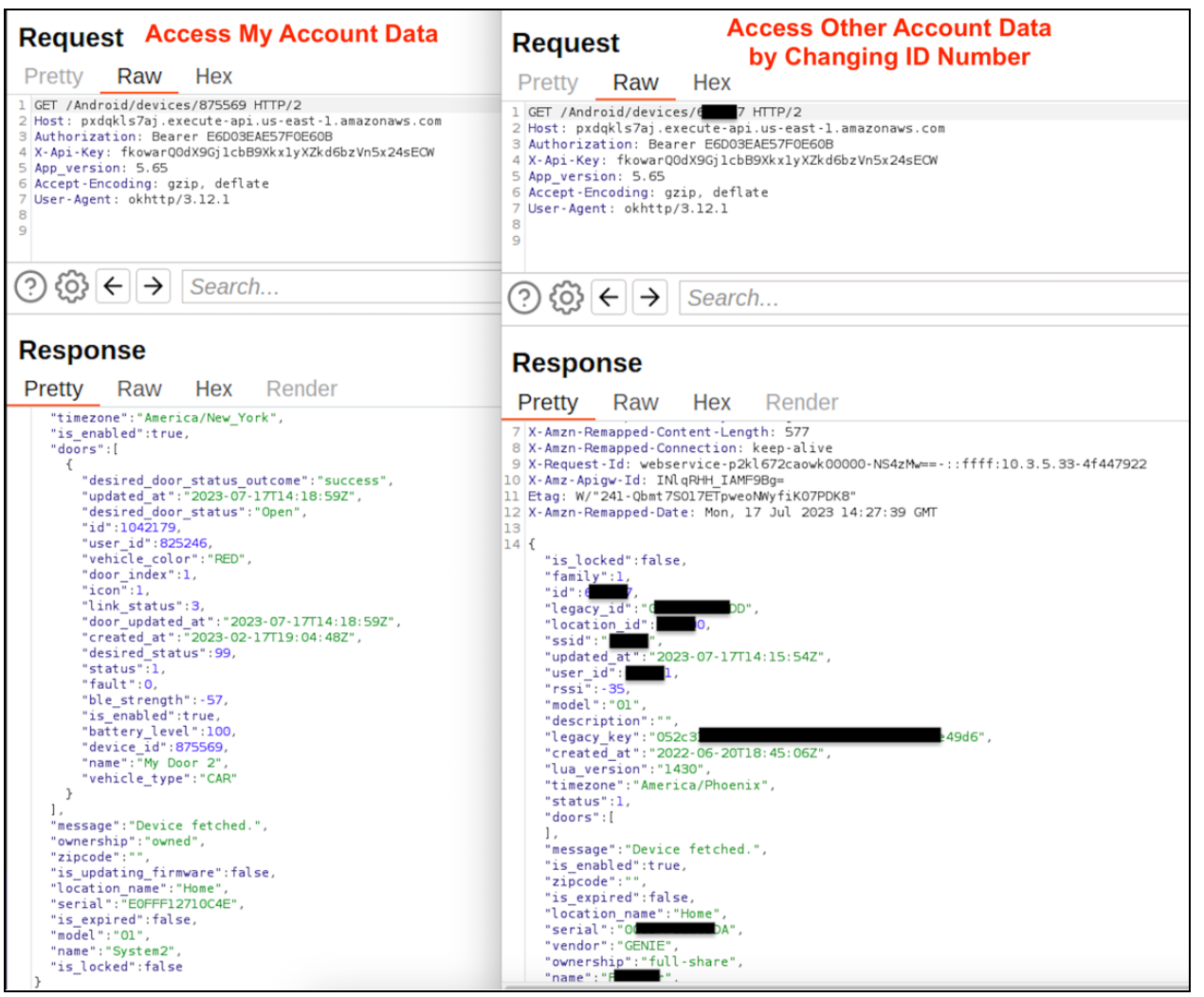
Additional Notes from the Vendor
This was resolved immediately after our internal penetration testing detected the issue. This happened because of a recent software update. The fix was applied to the API on 07/25/2023.
Mitigation: None
Article Tags
Related blog posts
Threat Research
New Whitepaper: Exploiting Cellular-based IoT Devices
Deral Heiland

Threat Research
Beyond the Device: Exploring the New Security Risks of Interconnected IoT at CES 2026
Deral Heiland

Threat Research
Threat Landscape of the Building and Construction Sector, Part One: Initial Access, Supply Chain, and the Internet of Things
Jeremy Makowski

Vulnerabilities and Exploits
Flashrom to Hexedit to Root: DEF CON 33 IoT Village Exercise
Rapid7