On January 21st 2017, Google's Project Zero disclosed a vulnerability in Cisco's WebEx browser plugin extension that could allow attackers to perform a remote code execution (RCE) exploit on any Windows host running the plugin.
An initial fix was pushed out by Cisco that warned a user if they were launching a meeting from a domain other than *.webex.com or *.webex.com.cn, however, the fix was questioned by April King from Mozilla based on the WebEx domain's security audit results from their Observatory project.
Cisco released a fix on 26th January 2017 that not only whitelisted the domains where meetings could be launched, but also tightened up the verification mechanisms to calls on DLLs, as observed by Tavis Ormandy at Project Zero, “It looks like they correctly handle Mac and Windows, and have also added some verification on GpcInitCall/GpcExitCall/etc so that functions have to match a RegEx. This looks like a huge improvement.”
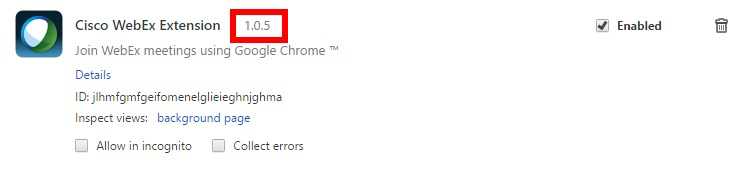
Full details of the vulnerability disclosure from Cisco can be found here. The following versions of plugins were declared vulnerable:
- < 1.0.7 on Google Chrome
- < 106 on Mozilla Firefox
- < 2.1.0.10 on Internet Explorer
Nexpose version 6.4.21 will allow you to detect if you have a vulnerable version of the Cisco WebEx plugin installed on any of your Windows hosts in your network and if you are vulnerable to CVE-2017-3823. As this is an authenticated check, credentials will need to be configured for the scan.
Article Tags
Related blog posts

Vulnerabilities and Exploits
CVE-2025-20333, CVE-2025-20362, CVE-2025-20363 - Multiple critical vulnerabilities affecting Cisco products
Ryan Emmons

Vulnerabilities and Exploits
CVE-2025-10035 - Critical unauthenticated RCE in GoAnywhere MFT
Stephen Fewer

Vulnerabilities and Exploits
CVE-2025-7775: Critical NetScaler vulnerability exploited in-the-wild
Stephen Fewer

Vulnerabilities and Exploits
CVE-2025-6543: Zero Day Exploitation of NetScaler ADC and NetScaler Gateway
Stephen Fewer