Last updated at Thu, 25 Jan 2024 01:59:17 GMT
Editor's Note: While this edition of the Metasploit Wrapup is a little late (my fault, sorry), we're super excited that it's our first ever Metasploit Wrapup to be authored by an non-Rapid7 contributor. We'd like to thank claudijd -long-time Metasploit contributor, Mozilla security wrangler, and overall nice guy - for writing this post. If other Metasploit contributors want to get involved with spreading the word, we want to hear from you!
We should be back on track timing-wise with our Wrapup for this week on Friday. Without any further delay, here's what's new in Metasploit versions 4.14.4 through 4.14.11.
- JE
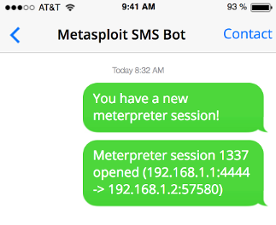
Here's my number, text me maybe?
Metasploit sessions can happen at any time. Fortunately, you can always be plugged in to what's going on with the new session notifier plugin, compliments of wchen. This plugin allows you to send SMS notifications for Metasploit sessions to a variety of carriers (AllTel, AT&T wireless, Boost Mobile, Cricket Wireless, Google Fi, T-Mobile, Version, and Virgin Mobile) so you'll never miss out on the pwnage.
Text-editors and Programming Languages
If you've ever been cornered by a VIM user around the water cooler and been regaled to exhaustion about why you should also choose VIM, you probably hold your ability to choose in high regard. Recently, acammack extended Metasploit to provide initial support to include more choice in what programming language you can write Metasploit modules in. The idea here would be that instead of being forced to write all modules in Ruby, you could write one in Python, Go, LOLCODE, or whatever your heart desires.
Improve Your Spider Sense
Many of us have had that feeling before that something doesn't add up, you can think of it as your own "hacker spider-sense." This can sometimes happen when you tell yourself, "that seemed way too easy" or "these services don't quite make sense", only to find out later that you've owned a honeypot. To help fight against this, thecarterb recently added an auxillary module to Metasploit, which allows you to check Shodan's honeyscore to see if your target is or is not known to act like a honeypot with a score between 0.0-1.0 (0.0 being not a honeypot and 1.0 being a honeypot). Having this data can be useful both after exploitation (to realize your blunder) or even earlier in the process to avoid an obvious honeypot before you send a single byte in its direction.
Waste Not, Want Not
You never know when a useful bit of information will be the key to another door. In that spirit, it's encouraged to loot as much as you can when you can. Recently, a number of useful modules have been added to help you loot as much as possible and improve your odds of success...
Multi Gather IRSSI IRC Passwords - This post module allows you to steal an IRSSI user's configuration file if it contains useful IRC user/network passwords. This could be helpful if you'd like to mix in a little social engineering, by impersonating your target to get additional people working for you.
Windows Gather DynaZIP Saved Password Extraction - This post module allows you to harvest clear text passwords from dynazip.log files. This can be pretty handy if you have have an encrypted zip file that you need opened in a hurry.
Multiple Cambium Modules - If you find yourself testing Cambium ePMP 1000's, you're in luck, as multiple modules have been added to effectively juice all sorts of information from these devices. These modules allow you to pull a variety of configuration files and password hashes over HTTP and SNMP. This is helpful to identify a shared password or password scheme that's been re-used on other network infrastructure devices to expand your influence.
New Modules
Exploit Modules (5 new)
- Cambium ePMP 1000 Arbitrary Command Execution by Karn Ganeshen
- Github Enterprise Default Session Secret And Deserialization Vulnerability by iblue and sinn3r
- SolarWind LEM Default SSH Password Remote Code Execution by Mehmet Ince
- Debian/Ubuntu ntfs-3g Local Privilege Escalation by jannh and h00die
- NETGEAR WNR2000v5 (Un)authenticated hidden_lang_avi Stack Overflow by Pedro Ribeiro
Auxiliary and post modules (10 new)
- Cambium ePMP SNMP Enumeration by Karn Ganeshen
- Cambium ePMP 1000 Password Hash Extractor by Karn Ganeshen
- Cambium ePMP 1000 Dump Device Config by Karn Ganeshen
- Cambium ePMP 1000 Login Scanner by Karn Ganeshen
- Multi Gather IRSSI IRC Password(s) by claudijd
- Moxa UDP Device Discovery by Patrick DeSantis
- Shodan Honeyscore Client by thecarterb
- Architecture Migrate by Koen Riepe
- Windows Gather DynaZIP Saved Password Extraction by Brendan Coles
- NETGEAR WNR2000v5 Administrator Password Recovery by Pedro Ribeiro
Get It
As always, you can update to the latest Metasploit Framework with msfupdate and you can get more details on the changes since the last blog post from GitHub:
To install fresh, check out the open-source-only Nightly Installers, or the binary installers which also include the commercial editions.