Bonjour!
Que désirez-vous?
We want to know what you'd like to see out of our latest Metasploit improvements. Please take a moment to fill out our community survey to help shape Metasploit's new backend data service. Tell us how you use the Metasploit database, which Metasploit data you use with other tools, how you need to store data from modules you've written, and so on. Please take our survey!
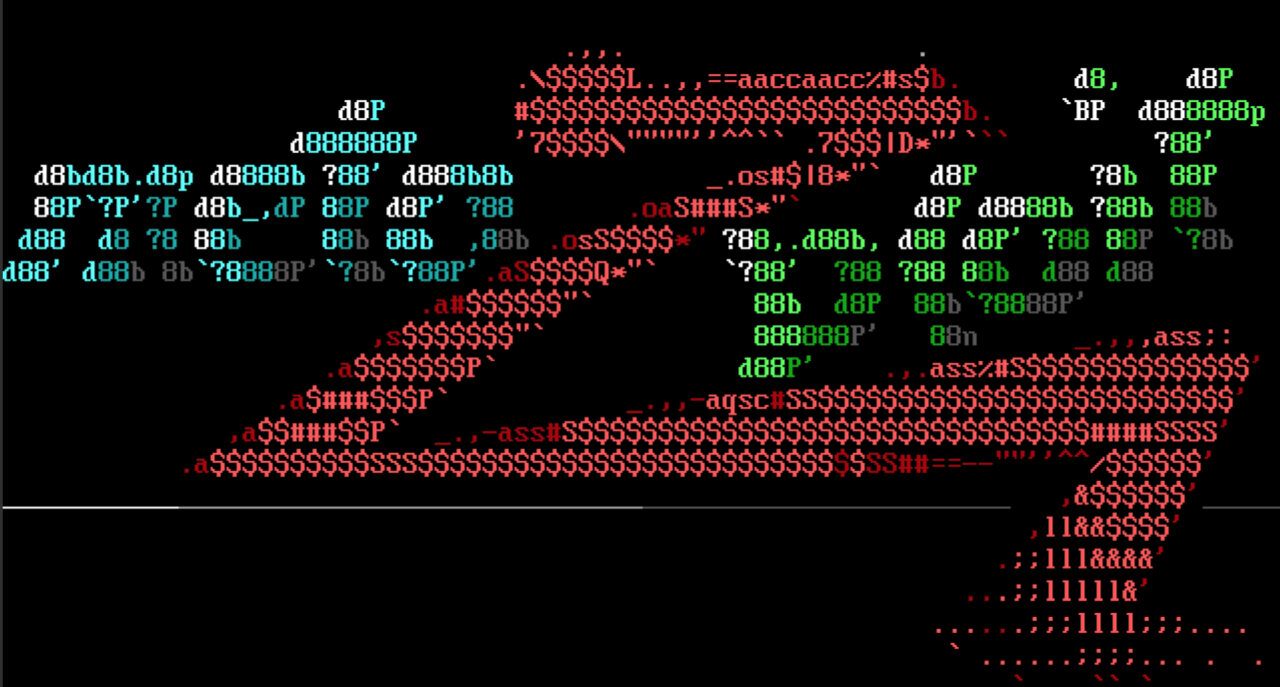
 Why pwn the DC?
Why pwn the DC?
Two legends team up, @OJ and @busterb, to update @gentilkiwi's Mimikatz Kiwi plugin to version 2.1.1 20180502. In addition, @OJ added the ability to dcsync and hashdump via Powershell, as well as adding streaming support to powershell commands to eliminate timeouts. Now you can dump all domain users without having to get onto the domain controller! Read up on the juicy details.
Linux RDS Privilege Escalation
@bcoles also submitted CVE-2010-3904 against in Linux' Reliable Datagram Sockets (RDS) protocol that provides a privilege escalation against kernel versions 2.6.30 to 2.6.36-rc8. It's been tested on Fedora and Ubuntu successfully -- head on over to the module documentation to see more.
 Linux AF_PACKET chocobo_root exploit
Linux AF_PACKET chocobo_root exploit

@bcoles submitted af_packet_chocobo_root_priv_esc, a privilege escalation for Ubuntu-based systems by exploiting a use-after-free vulnerability in the Linux kernel (CVE-2016-8655). The vulnerability was present for 5 years, but there are a few caveats, so tread lightly.
telpho10, now with more vulnerable
@whoot returned to their first Metasploit contribution to report that telpho10_credential_dump is still working on new versions. The version limitation check has been removed, since all versions of the Telpho10 ISDN+VOIP telephone system appliance are vulnerable to credential dumping. Bon Appétit!
 Meanwhile, in France
Meanwhile, in France

@ClementNotin noticed that French versions of Windows refer to the SYSTEM account as Système. (hon hon hon) Their quick fix to check the SID, rather than the username, improves post-exploit account detection on international systems, and cleans up some code in the process! Thanks @ClementNotin!
Big things come in small changes
Rapid7's own pentest team mentioned that they'd like to be able to control whether the auxiliary/scanner/http/cisco_ssl_vpn module checked credentials against the default empty group. As a result of these sometimes unnecessary checks, accounts can be locked out during a test. So @busterb added an 'EMPTYGROUP' option to the module (defaulting to false) to help prevent unnecessary pentesting sadness.
New Modules
Exploit modules (2 new)
- exploits/linux/local/libuser_roothelper_priv_esc was submitted by Brendan Coles (@bcoles).
- exploit/linux/local/rds_priv_esc was also submitted by Brendan Coles (@bcoles).
Improvements
- auxiliary/admin/http/telpho10_credential_dump was updated by Jan Rude (@whoot).
- Support for External exploit module functionality to run a check if the target is vulnerable, was added by @acammack-r7.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate and you can get more details on the changes since the last blog post from GitHub:
To install fresh, check out the open-source-only Nightly Installers, or the binary installers which also include the commercial editions. PLEASE NOTE that these installers, and Metasploit Framework versions included in distros such as Kali, Parrot, etc., are based off the stable Metasploit 4 branch. If you'd like to try out the newer things going into Metasploit 5, that work is available in the master branch of the [Metasploit Framework repo][repo] on GitHub.