One of the goals of InsightIDR is to be that single pane of glass across your detection and response lifecycle. The core that powers this is user behavior analytics (UBA), which detects anomalous authentications and behavior and enriches your log data with user context. We’d like to announce a new way to collect log data: Universal Event Formats.
Here is a quick Q&A featuring myself and Principal Security Consultant Teresa Copple, whose team delivers InsightIDR Quick Start to customers:
Q: What formats does Rapid7 offer as part of Universal Event Formats?
A: Available today, we are now offering four formats: DHCP, VPN, Antivirus, and Ingress Authentication.
Q: Tell me more about the Ingress Authentication Universal Event format.
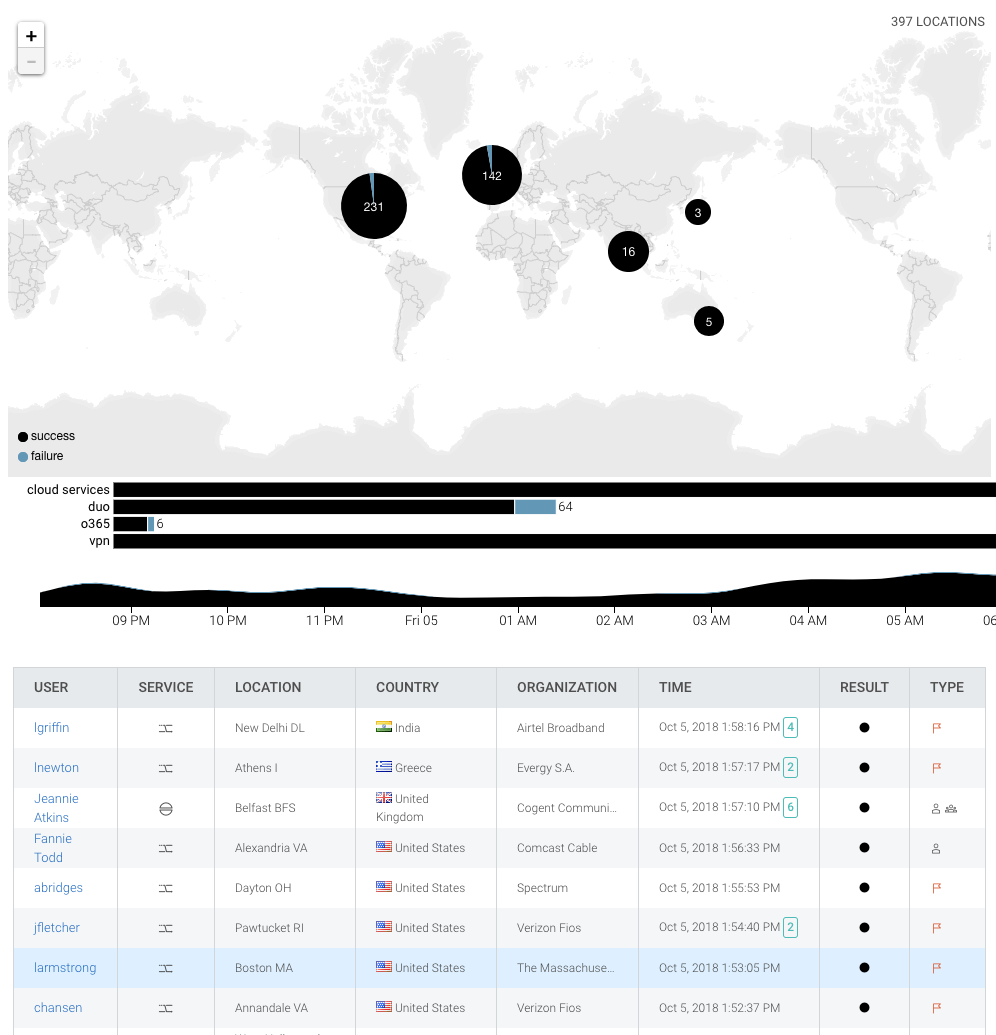
A: Any authentication activity, whether it is to access an internal service (such as LogMeIn Pro) or a third-party service (such as Oracle Identity Cloud) that stores internal proprietary data, may be represented with an Ingress Authentication Universal Event Format. InsightIDR will correlate and analyze these authentications to identify anomalous behavior such as Multiple Country Authentications and Ingress from Disabled Accounts, and to power your Ingress Locations map and investigations in Log Search.
Q: What if I have special VPN software that is older or obscure?
A: No problem! You can use the VPN Universal Event Format to send that data to InsightIDR. We will apply UBA just like we provide on natively supported event sources to give you the attribution and the details you love.
Q: What’s the difference between UEF and the Raw Data event source in InsightIDR?
A: Currently, InsightIDR supports several types of “Raw Data,” including Generic Syslog, Generic Windows Event Log, Custom Logs, and Database Audit Logs. This allows you to collect almost any type of log from any device with InsightIDR. With Raw Data, you get log search and dashboards, but they aren’t analyzed for user behavior and applied against your user baselines. When you convert the raw data to a supported UEF, you then get the detection, user attribution, and investigative context.
Q: What’s your suggested log manipulation tool?
A: Any tool that will allow you to accept incoming log data, manipulate it into UEF, and forward it to InsightIDR may be used. We recommend NXLog or Logstash. NXLog is available in both a free community edition and commercial enterprise edition. The community edition will typically work fine for our purposes and may be used. The commercial version is more feature-rich and flexible, which may make it easier for you to manipulate your logs. Logstash is an open source tool for collecting, transforming, and sending logs into a “stash,” which in this case will be your InsightIDR collector.
Q: What’s all of this going to cost?
A: These UEFs are available at no additional cost, so if you have a previously unsupported DHCP, VPN, Antivirus, or Ingress Authentication date source, check out our universal event sources documentation pages and give it a shot!
We will be releasing support for more sources in the future, as well as a follow-up blog next week that will map out a step-by-step plan for converting your raw logs into UEF. If you have any questions, let us know—we want to hear about your interesting use cases and ensure you are set up for success.
Article Tags
Related blog posts

Detection and Response
Top Challenges for Security Analytics and Operations, and How a Cloud-Based SIEM Can Help
Margaret Wei
![[Q&A] Why Every Threat Detection Strategy Needs User Behavior Analytics](/_next/image/?url=%2Fblog-post-image-placeholder.webp&w=1920&q=75)
Detection and Response
[Q&A] Why Every Threat Detection Strategy Needs User Behavior Analytics
Christie Ott

Detection and Response
Universal Event Formats in InsightIDR: A Step-by-Step NXLog Guide
Teresa Copple

Detection and Response
SIEM Market Evolution And The Future of SIEM Tools
Matt Hathaway