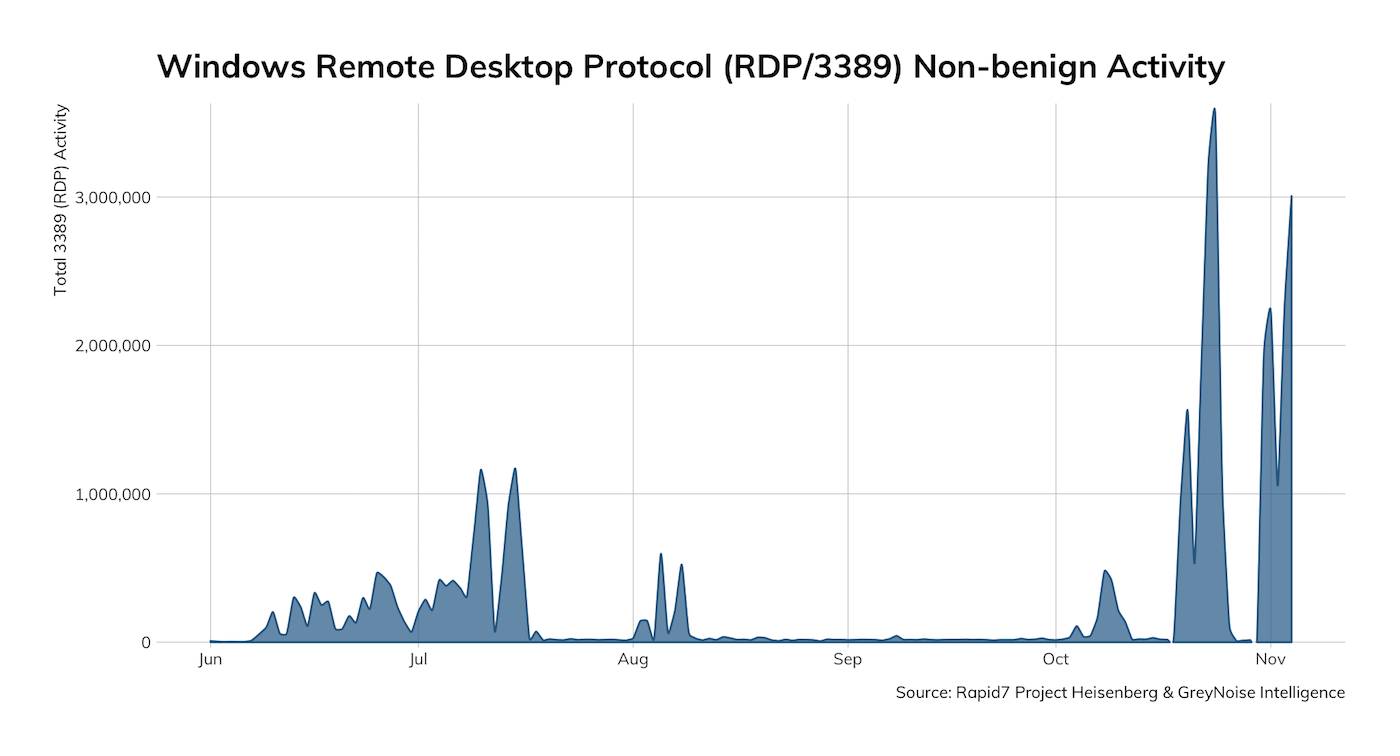
A critical vulnerability called “BlueKeep” put Remote Desktop Protocol (RDP) security on everyone’s radar earlier this year. Just a few months later, Microsoft announced a related vulnerability, DejaBlue. RDP exploits are no joke—Rapid7’s Project Sonar estimates that around 900,000 workstations and servers running RDP around the world are vulnerable. And, since Nov. 1, Rapid7’s Project Heisenberg caught 12,949 unique IPv4s, with endpoints in the Netherlands, Italy, and France accounting for nearly 70% of the unique sources.
Recently, I joined Randy Franklin Smith from Ultimate IT Security to talk about BlueKeep, DejaBlue, and the potential for further RDP exploits. In the webcast, we discussed the lessons you can learn from these exploits, how to protect your organization, and how Rapid7 InsightVM can help in the fight against BlueKeep and similar vulnerabilities.
How BlueKeep works
According to Randy, the attack on RDP was long overdue. RDP is a complex, functionally rich protocol, which means it has a large attack surface. It was only a matter of time before hackers turned their attention to the protocol’s weaknesses. We know about BlueKeep, which affects Windows 2008 R2 and earlier, and DejaBlue, which affects newer systems, but there will probably be more to come.
BlueKeep seeks to run malicious code in the kernel memory of the server, allowing the hacker to take control of the entire system. The key to sending this code to the server is in the session setup. It’s at this point that BlueKeep sends arbitrary code to the server. The server stores it in memory, then frees the memory up again. However, because the server retains a pointer to the memory, BlueKeep is able to execute the malicious code.
Clearly, moving authentication in front of session setup would be valuable in combating BlueKeep and DejaBlue. Network Level Authentication (NLA), an RDP enhancement, does just that. However, NLA can’t entirely prevent RDP vulnerabilities like BlueKeep. If attackers have non-privileged credentials, they could still log into RDP. As the session is built up, the attacker could use BlueKeep to perform privilege elevation.
Lessons learned from BlueKeep and DejaBlue
The first takeaway from these recent RDP vulnerabilities is to upgrade and update your systems. Vulnerabilities, including BlueKeep, often target older systems.
Patching is the oldest trick in IT security, but it remains critical. Your patch process will take care of most of your systems, but it’s not enough. Vulnerability assessment steps up to find the places where the patch process has failed. Remember, it only takes one vulnerable server to give the attackers a way in.
Another lesson to keep in mind is that the risk of a vulnerability can change over time. When BlueKeep was first announced, it was purely theoretical. There was no proof-of-concept and no reports of the vulnerability being exploited. However, once it was discovered, it became a race for hackers to figure out how to use BlueKeep before potential victims patched their systems. In other words, the risk level rose as time went on.
The final lesson that Randy suggested we learn from BlueKeep is that multi-factor authentication (MFA) is not a silver bullet. In fact, no security technology is. In the case of BlueKeep, the malicious code is injected before MFA even takes place.
How to protect against RDP vulnerabilities
There’s always some level of risk involved with exposing RDP to untrusted connections, but having the right tools will greatly mitigate the danger. In addition to NLA, there are several solutions that can make you less vulnerable to RDP exploits, including:
- VPN
- Remote Desktop Gateway
- Privileged Session Proxies
- IP Restrictions
- Monitoring
How Rapid7 InsightVM can help
InsightVM, Rapid7’s vulnerability management solution, can give you clarity into assets impacted by RDP vulnerabilities like BlueKeep and DejaBlue (along with other vulnerabilities too!). InsightVM will discover all of your assets, whether they are on-premises machines, cloud servers, IoT devices, or something else. Rapid7’s Project Sonar enables customers to get clarity of internet-facing assets (most susceptible to RDP attacks) that may have been missed, and prioritize their remediation higher on the list.
Speaking of prioritization, once we’ve successfully identified all our assets and their vulnerabilities we have to make the difficult decisions about how we are going to direct our limited resources. InsightVM’s Active Risk score provides an actionable, 1–1000 scale based on the likeliness of an attacker exploiting a given vulnerability in a real attack. Remember how the BlueKeep vulnerability became a greater risk over time? The Real Risk score takes that into account. Factors like the age of the vulnerability, whether or not a proof-of-concept exists, and the skill level required to take advantage of the exploit, and standard CVSS score are all part of the Real Risk score calculation.
Finally, all of this work is for nothing if we don’t do the work of implementing compensating controls (like NLA) or patching. InsightVM is focused on helping you create the influence you need to work with your counterparts in IT and development to move this work forward and make measurable progress. Integrations with their ticketing solutions like ServiceNow and JIRA, along with their patching tools like SCCM and BigFix ensures that you meet them where (and how) they work.
With InsightVM, Security can effectively identify, prioritize, and remediate vulnerabilities while extending their influence and aligning technical teams to reduce risk and accelerate progress towards common goals.
Related blog posts

Vulnerabilities and Exploits
CVE-2026-0265: Authentication Bypass in Palo Alto Networks PAN-OS
Rapid7

Vulnerabilities and Exploits
Critical Buffer Overflow in Palo Alto Networks PAN-OS User-ID Authentication Portal (CVE-2026-0300)
Jonah Burgess

Products and Tools
Negotiating with the Board: Translating Active Risk into Financial Exposure
Trevor Christiansen

Vulnerabilities and Exploits
CVE-2025-20333, CVE-2025-20362, CVE-2025-20363 - Multiple critical vulnerabilities affecting Cisco products
Ryan Emmons
