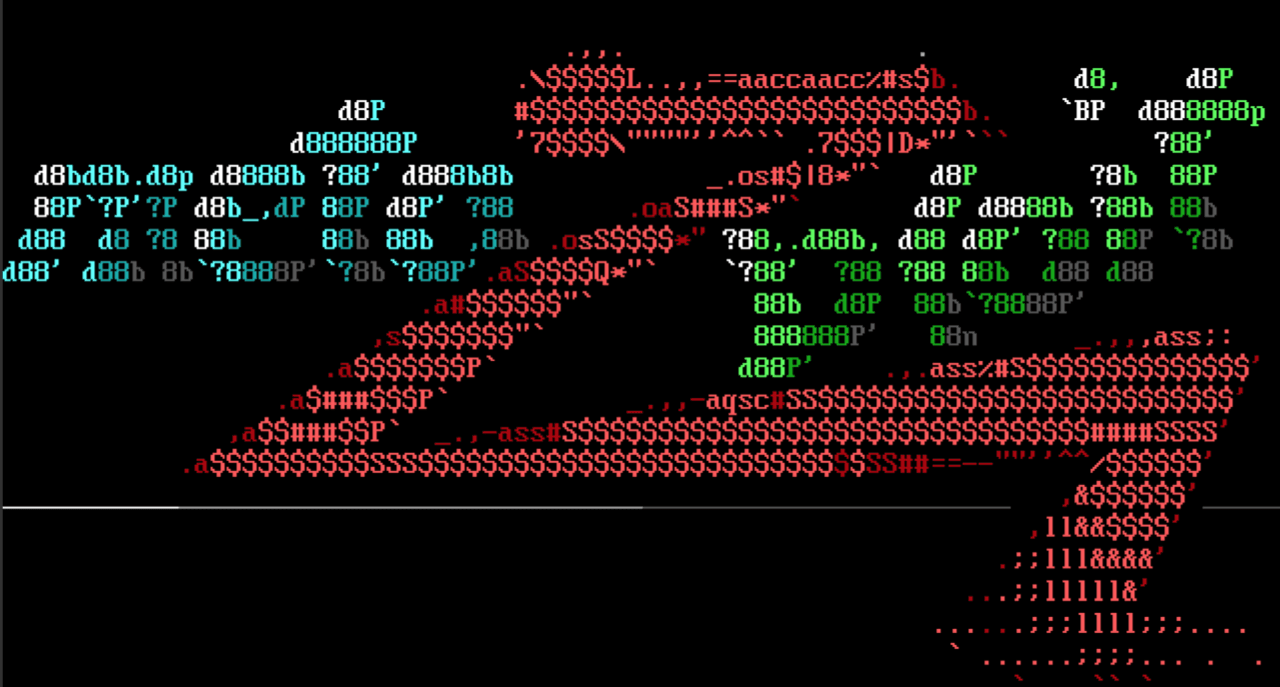
Credential gatherers, mix-ins, oh my!
We're excited that Metasploit now includes support for 28 related post modules for gathering credentials based on the PackRat toolset. This is a continuation of #5433, #11700, and #11719. It was developed by community contributors Kazuyoshi Maruta, Daniel Hallsworth and Barwar Salim M, for their final year projects at Leeds Beckett University with guidance, code clean-up and some additions by Z. Cliffe Schreuders.
We thank these community contributors for their months of effort and patience while getting so many modules through the code review process.
Netgear PNPX_GetShareFolderList Authentication Bypass
This auxiliary module exploits an authentication bypass in a range of different Netgear router models and firmware versions. The module leverages this vulnerability to log in as the admin user and then achieves a telnet session as root through the auxiliary/scanner/telnet/telnet_login module.
Read more about the SSD Netgear D7000 authentication bypass advisory here.
New module content (30)
- Netgear PNPX_GetShareFolderList Authentication Bypass by Grant Willcox and Unknown - The auxiliary/admin/http/netgear_pnpx_getsharefolderlist_auth_bypass module exploits an authentication bypass in various Netgear router models running firmware versions prior to 1.2.0.88, 1.0.1.80, 1.1.0.110, and 1.1.0.84. The module leverages the vulnerability to log in as the admin user and then achieves a telnet session as the root user through the auxiliary/scanner/telnet/telnet_login module.
- ECU Hard Reset by Jay Turla - Adds a new ecu_hard_reset hardware module which performs a hard reset in the ECU Reset Service Identifier (0x11)
- 28 "PackRat" credential gatherers by Barwar Salim M, Daniel Hallsworth, Kazuyoshi Maruta (@KazuCyber), and Z. Cliffe Schreuders (@cliffe) - This pull request adds 28 post-exploitation modules, based on a common mixin, known as PackRat, which gathers file and information artifacts from end users’ systems.
- Aim credential gatherer
- Chrome credential gatherer
- Comodo credential gatherer
- Coolnovo credential gatherer
- Digsby credential gatherer
- Flock credential gatherer
- Gadugadu credential gatherer
- ICQ credential gatherer
- Ie credential gatherer
- Incredimail credential gatherer
- KakaoTalk credential gatherer
- Kmeleon credential gatherer
- LINE credential gatherer
- Maxthon credential gatherer
- Miranda credential gatherer
- Opera credential gatherer
- Operamail credential gatherer
- Postbox credential gatherer
- QQ credential gatherer
- Safari credential gatherer
- Seamonkey credential gatherer
- Srware credential gatherer
- Tango credential gatherer
- Thunderbird credential gatherer
- Tlen credential gatherer
- Viber credential gatherer
- Windows Live Mail credential gatherer
- Xchat credential gatherer
Enhancements and features
- #15441 from bf9114 - This change extends the Meterpreter search functionality by adding the ability to search by modified dates across all supported Meterpreter platforms. This allows a user to quickly find files on a target system that has been modified recently, or within a specific date range.
- #15594 from h00die - This adds options to the wordpress_scanner that enables the user to only scan for wordpress themes or plugins that Metasploit has modules for.
- #15630 from zeroSteiner - This adds the option DB_SKIP_EXISTING to the AuthBrute mixin to give users the option to skip credentials already in the database when performing brute force attacks.
- #15669 from adfoster-r7 - Updates the multi/manage/screenshare module to use the Espia screenshot capabilities if present, and to gracefully fallback to using the normal screenshot behavior if it fails to load as expected.
- #15721 from zeroSteiner - Support has been added into Metasploit for negotiating SSL connections over multiple connections types including Meterpreter and SSH. As a result, users can now make HTTPS requests over pivoted sessions. Previously, if users tried to make such connections, they would be sent via plaintext instead of being SSL encrypted.
- #15722 from adfoster-r7 - The rerun command has been enhanced to support tab completion.
- #15726 from zeroSteiner - This adds the MeterpreterTryToFork option to the Mettle payloads. When set, it translates to Mettle's :background option. When :persist is not configured it will attempt to fork the stage into the background.
Bugs fixed
- #15703 from space-r7 - This updates payload/windows/x64/encrypted_shell/reverse_tcp to no longer crash on MacOS. Additionally adds an advanced option, ShowCompileCMD, that prints the compilation command used.
- #15720 from NeffIsBack - This fixes a bug where the rhost value was incorrectly passed to the underlying scanning script, resulting in an abnormal exit.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate and you can get more details on the changes since the last blog post from GitHub:
If you are a git user, you can clone the Metasploit Framework repo (master branch) for the latest. To install fresh without using git, you can use the open-source-only Nightly Installers or the binary installers (which also include the commercial edition).