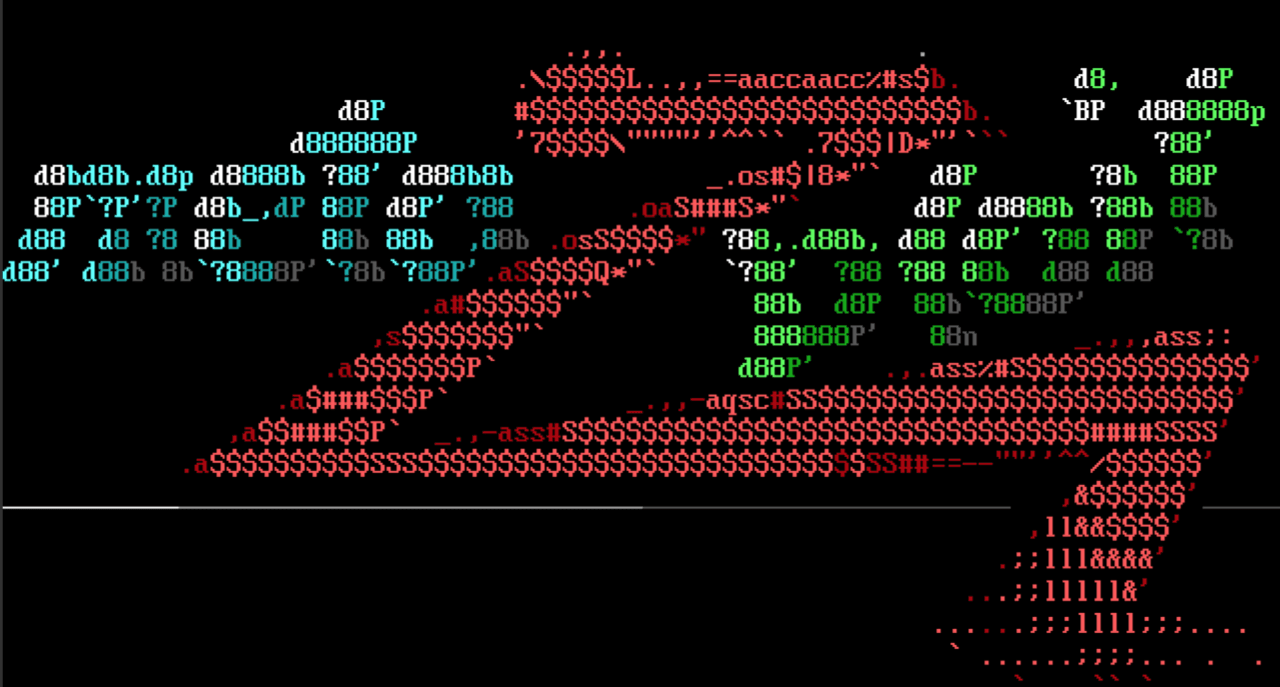
Dump Windows secrets from Active Directory
This week, our very own Christophe De La Fuente added an important update to the existing Windows Secret Dump module. It is now able to dump secrets from Active Directory, which will be very useful for Metasploit users. This new feature uses the Directory Replication Service through RPC to retrieve data such as SIDs, password history, Domain user NTLM hashes and Kerberos keys, etc. This replicates the behavior of the famous impacket secretsdump.py, with the benefit of being fully integrated with Metasploit Framework. For example, it is possible to pivot on a compromised host and run the Windows Secret Dump module against an internal Domain Controller directly from msfconsole. Furthermore, the secrets are stored in the internal database, which lets other modules access this information easily.
This update also brings another big improvement to the ruby_smb library. This adds a new DCERPC client and many ready-to-use RPC queries from Directory Replication Service (DRS) Remote Protocol, Security Account Manager (SAM) Remote Protocol and Workstation Service Remote Protocol. These will greatly simplify the process of writing modules that use DCERPC against Windows systems.
Authenticated Catch Themes Demo Import Remote Code Execution
Thank you to Ron Jost, Thinkland Security Team, and h00die for their community contribution of a Remote Code Execution exploit module against versions 1.8 and earlier of the Catch Themes Demo Import Wordpress Plugin.
New module content (6)
- Grafana Plugin Path Traversal by h00die and jordyv, which exploits CVE-2021-43798 - This aAdds a module to exploit Grafana file read vulnerability CVE-2021-43798.
- Native LDAP Server (Example) by RageLtMan and Spencer McIntyre - This adds the initial implementation of an LDAP server implemented in Rex and updates the existing log4shell scanner module to use it as well as provides a new example module.
- Wordpress Plugin Catch Themes Demo Import RCE by Ron Jost, Thinkland Security Team, and h00die, which exploits CVE-2021-39352 - This adds an exploit for the Catch Themes Demo Import Wordpress plugin for versions below 1.8. The functionality for importing a theme does not properly sanitize file formats, allowing an authenticated user to upload a php payload. Requesting the uploaded file achieves code execution as the user running the web server.
- Wordpress Popular Posts Authenticated RCE by Jerome Bruandet, Simone Cristofaro, and h00die, which exploits CVE-2021-42362 - This PR adds a new exploit for wp_popular_posts <=5.3.2.
- ManageEngine ServiceDesk Plus CVE-2021-44077 by wvu and Y4er, which exploits CVE-2021-44077
- Dell DBUtilDrv2.sys Memory Protection Modifier by Jacob Baines, Kasif Dekel, Red Cursor, and SentinelLabs - This module leverages a write-what-where condition in DBUtilDrv2.sys version 2.5 or 2.7 to disable or enable LSA protect on a given PID (assuming the system is configured for LSA Protection). The drivers must be provided by the user.
Enhancements and features
- #15831 from zeroSteiner - Established SSH connections can now leverage the pivoting capabilities of the SshCommandShellBind session type.
- #15882 from smashery - An update has been made which will prevent exploits from running a payload if the exploit drops files onto the target, but the payload doesn't have the capability to clean those dropped files up from the target. Users can still override this setting by specifying set AllowNoCleanup true if they wish to bypass this protection.
- #15924 from cdelafuente-r7 - This adds the NTDS technique to the Windows Secrets Dump module, enabling it to be used against Domain Controllers. It also pulls in RubySMB changes that include many DCERPC related improvements and features.
- #15986 from bcoles - Module notes added to bash_profile_persistence now describe impacts of utilizing the module in a target environment.
Bugs fixed
- #15982 from 3V3RYONE - This fixes a bug where modules using the SMB client would crash when the SMBUser datastore option had been explicitly unset.
- #15984 from h00die - This PR fixes a bug in the snmp library which caused it to ignore version 1, despite specifically set options.
- #16003 from jmartin-r7 - This fixes an issue with GitHub actions where the Ruby 3.1.0 version string is not yet being parsed correctly leading to automation failures.
- #16015 from zeroSteiner - This fixes a regression in tab completion for the RHOSTS datastore option.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate
and you can get more details on the changes since the last blog post from
GitHub:
If you are a git user, you can clone the Metasploit Framework repo (master branch) for the latest.
To install fresh without using git, you can use the open-source-only Nightly Installers or the
binary installers (which also include the commercial edition).