Posts tagged Endpoint Security
Products and Tools
Velociraptor 0.6.9 Release: Digging Even Deeper with SMB Support, Azure Storage and Lockdown Server Mode
Mike Cohen

Detection and Response
Cybersecurity as Digital Detective Work: DFIR and Its 3 Key Components
Jesse Mack

Detection and Response
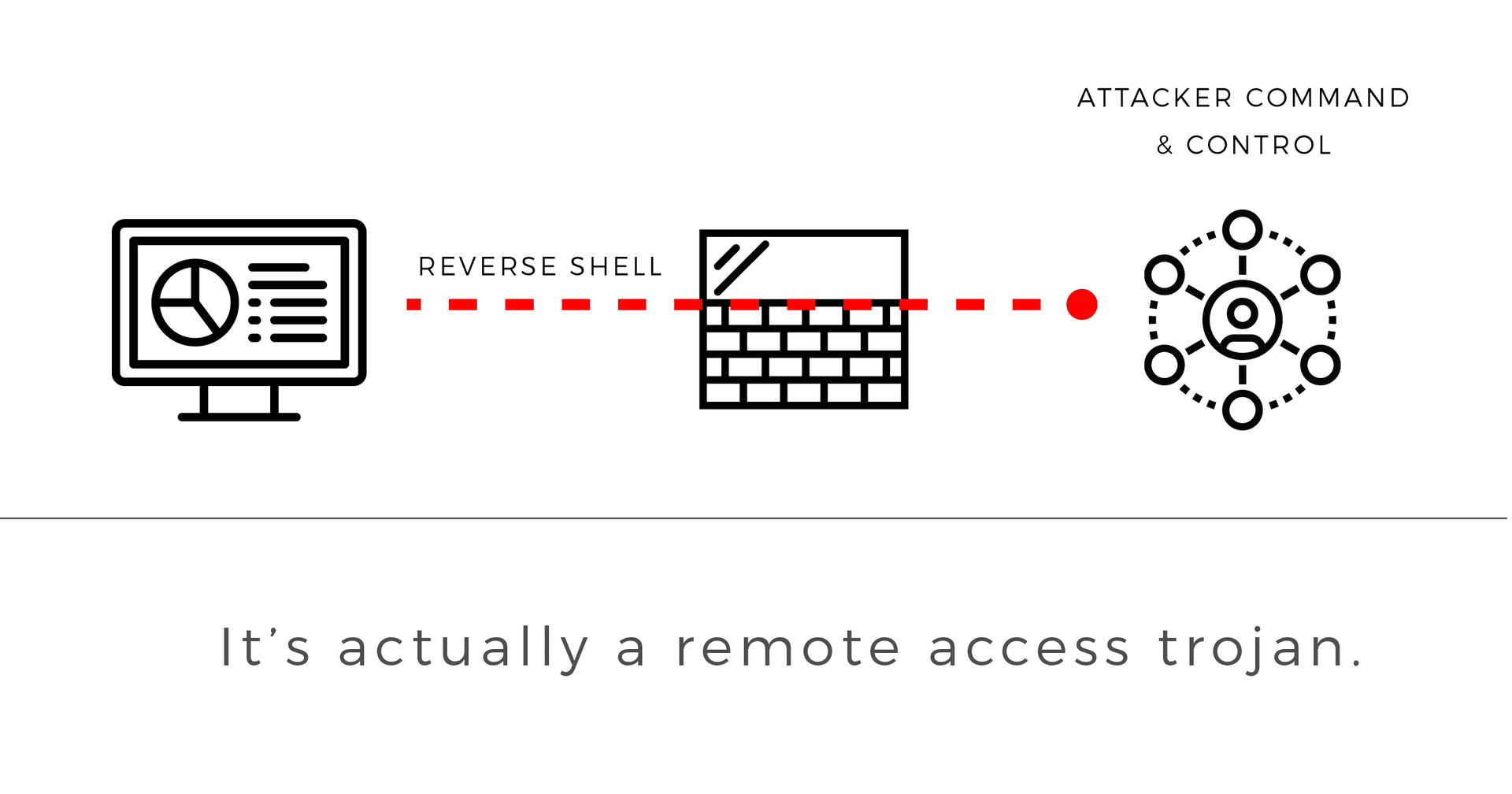
Endpoint Agents Are Necessary for Today’s Modern Environment: Here’s Why (Part 2)
Vivian Ma

Detection and Response
Endpoint Agents Are Necessary for Today’s Modern Environment: Here’s Why (Part 1)
Vivian Ma
Products and Tools
Why Managed Detection and Response Zeroes In On the Endpoint
Eric Sun

Exposure Management
Live Vulnerability Monitoring with Agents for Linux
Ken Mizota

Security Operations
Addressing the issue of misguided security spending
kevinbeaver

Detection and Response
macOS Agent in Nexpose Now
Ken Mizota

Detection and Response
Announcing InsightOps - Pioneering Endpoint Visibility and Log Analytics
Trevor Parsons

Exposure Management
Live Monitoring with Endpoint Agents
Jane Man

Detection and Response
IDC: 70% of Successful Breaches Originate on the Endpoint
Christian Kirsch

Detection and Response
How to use Nexpose to find all assets affected by DROWN
Joakim Kennedy