Running Malicious Code in Safari
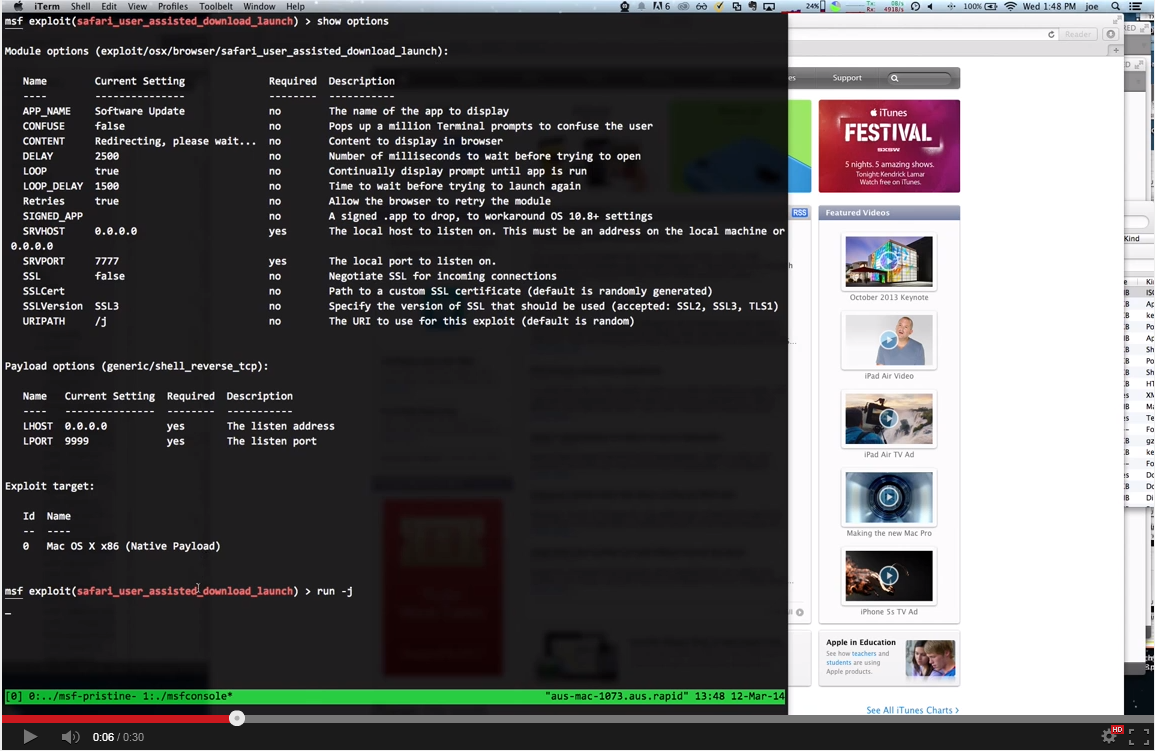
The most fun module this week, in my humble opinion, is from Rapid7's own Javascript Dementor, Joe Vennix. Joe wrote up this crafty implementation of a Safari User-Assisted Download and Run Attack, which is not technically a vulnerability or a bug or anything -- it's a feature that ends up being a kind of a huge risk. Here's how it goes:
The target user is already running some decently recent version of Apple OS X, which means they have the Gatekeeper control installed. Gatekeeper is supposed to "protect your Mac" from "malware and misbehaving apps downloaded from the Internet." It does this by warning the user against downloading apps from untrusted (non-Apple-controlled) sources.
Since your target user is all hip and not afraid of these warnings (maybe she's a habitual open source / non-Apple-sourced user of software), clicking "Open" at this point will automatically download and execute the downloaded app, which, in our case, is an OSX payload. In the event the user is more paranoid (but more on that below), that's okay -- the exploit will just ask again. And again. And again. Forever. There is no escaping the "Okay" button.
Ta-da, shells! For a silent film produced by the Vennix himself, please see This link or just click on the screenshot over there.
Therein lies the rub -- Apple is warning people that all software sourced on the non-blessed Internet is potentially evil, and therefore, every non-blessed download engenders this warning. This disregards the reality that only some (small!) fraction of software from the Internet is actually evil. As a result, this warning is inevitably going to fall on deaf ears, thanks to the Crying Wolf problem that end-user software is notorious for.
This is the same kind of psychological user interface problem that endless warnings about self-signed, mismatched, and out-of-date SSL certificates cause for browsers. Yes, "bad" certs like this are potentially evil. Yes, users should use caution when encountering such certs. However, there's no reasonable course of action to actually behave cautiously. What are you going to do, not visit the website you had your heart set on? Besides, every user's experience with these warnings is that the vast majority of the time, nothing bad actually happens when they click "Ok." This ends up giving people literally years of training that warnings like this are an annoyance at best, and flat out wrong at worst.
Point of story, this module takes advantage of a bug in human risk assessment. I don't know where to report these bugs (I don't think CERT/CC is a good place for meatware bugs). In any case, have fun patching against this, vendors and IT shops.
I know this opinion on secure software design isn't terribly groundbreaking, but this is still a problem here on the 21st Century Internet. So, while Apple, Microsoft, Google, and the rest can noodle on this for a while longer, feel free to use this module to demonstrate the actual risk of this risky design decision.
New Modules
This week's release includes nine new modules, including the three new Yokogawa SCADA modules mentioned in Juan's disclosure on the same and discussed last weekend at RootedCon. There hasn't been a lot of media pickup on those, but the usual warnings apply: if you're responsible for SCADA/ICS (industrial control systems), please pretty please check to see if you're vulnerable, and regardless of the answer, get those things off the public Internet. Nobody wants their oil and gas pipelines monkeyed with by Anonymous or whomever.
Exploit modules
- Safari User-Assisted Download and Run Attack by joev
- ALLPlayer M3U Buffer Overflow by Gabor Seljan, Mike Czumak, and metacom exploits OSVDB-98283
- Windows Escalate UAC Protection Bypass (In Memory Injection) by Ben Campbell, David Kennedy "ReL1K", mitnick, and mubix
- HP Data Protector Backup Client Service Remote Code Execution by juan vazquez and Aniway.Anyway exploits ZDI-14-008
- SolidWorks Workgroup PDM 2014 pdmwService.exe Arbitrary File Write by Brendan Coles and Mohamed Shetta exploits OSVDB-103671
- Yokogawa CENTUM CS 3000 BKBCopyD.exe Buffer Overflow by juan vazquez and Redsadic
- Yokogawa CENTUM CS 3000 BKHOdeq.exe Buffer Overflow by juan vazquez and Redsadic
Auxiliary and post modules
- Yokogawa CENTUM CS 3000 BKCLogSvr.exe Heap Buffer Overflow by juan vazquez and Redsadic
- MantisBT Admin SQL Injection Arbitrary File Read by Brandon Perry and Jakub Galczyk exploits CVE-2014-2238
If you're new to Metasploit, you can get started by downloading Metasploit for Linux or Windows, either the totally free Metasploit Community Edition, or the 7-day free trial of Metasploit Pro. If you're the sort to track bleeding-edge development code, then these modules are but an msfupdate command away. For readers who are already using Metasploit Community or Metasploit Pro, you'll be able to install the new hotness today via the Administration : Software Updates button.
For additional details on what's changed and what's current, please see Brandont's most excellent release notes.
Article Tags
Related blog posts

Vulnerabilities and Exploits
Metasploit Weekly Wrap-Up 7/19/2024
Christophe De La Fuente

Vulnerabilities and Exploits
Metasploit Weekly Wrap-Up: Mar. 4, 2022
Shelby Pace

Vulnerabilities and Exploits
The Everyperson’s Guide to Log4Shell (CVE-2021-44228)
boB Rudis

Threat Research
Metasploit Wrap-Up 12/10/21
Jeffrey Martin
