In this third installment of our series around 2021 security planning, we’re focused on SOC automation. In part one, we spoke with Rapid7 Detection and Response Practice Advisor, Jeffrey Gardner on tips and advice for ramping up annual security planning. In part two, we discussed how reliable, comprehensive detections lead to SOC efficiency and drive security programs forward. In this installment, we’ll discuss how automation is critical for accelerating and streamlining incident response in today’s complex security environments.
Current state of security
This past year, the security landscape has become more dispersed than ever before, with more than 92% of organization’s IT environments at least somewhat in the cloud—and with the current surge in remote work, it doesn’t seem like this will be slowing down any time soon.
The more widespread assets and users become across an environment, the more there is for security teams to stay on top of, from the influx of data and alerts to the manual tasks analysts are faced with while investigating and responding to incidents. It’s not only exhausting, but it impedes efficiency, especially for under-resourced teams. To effectively monitor modern environments and accelerate incident response, using SIEM and SOAR together is key. As teams prepare for 2021, many may be looking to introduce or expand automation capabilities to streamline processes across their organization.
Level up your detection and response with Rapid7’s SIEM + SOAR technology
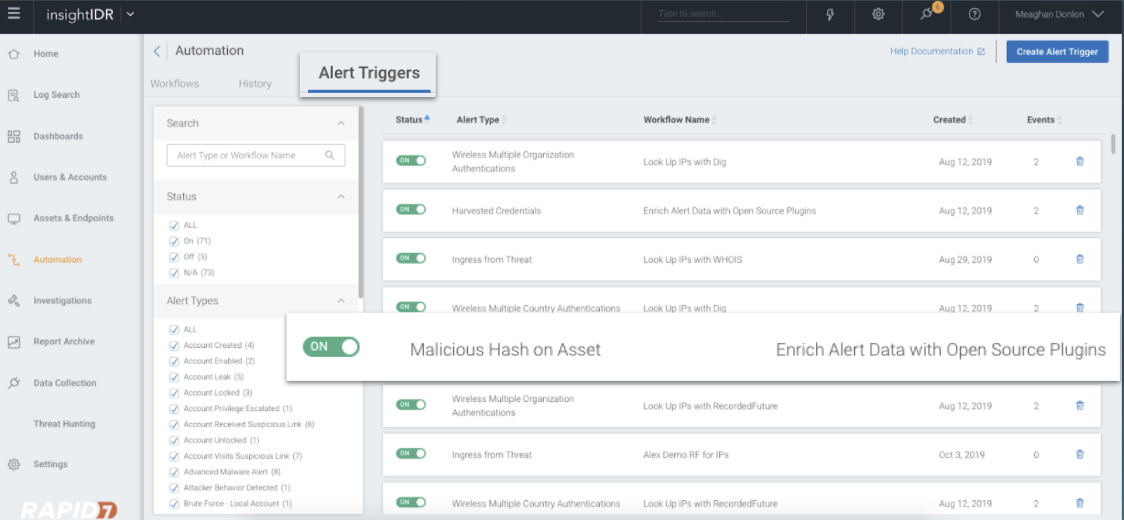
InsightIDR, Rapid7’s cloud SIEM, ingests and analyzes critical security data from across an organization’s environment—including user activity, logs, cloud, endpoints, and network traffic—into a single solution. Then, with its expert-driven detections and automation, it enables security teams to respond to attacks in a fraction of the time. Using pre-built automation workflows, customers can take actions like containing threats on an endpoint, suspending user accounts, or integrating with ticketing systems, all from within InsightIDR.
Security Planning Tip: In planning, a good step to figuring out where to begin with automation might be looking at where analysts are spending the bulk of their time, but not seeing a large return on that investment. For example, onboarding new employees with the right permissions and account configuration is a time consuming but necessary security step. With automation, you can give your team hours back and help ensure a streamlined, consistent process across all new hires.
But that’s just the beginning—for InsightIDR customers looking to uplevel their automation capabilities, adding on InsightConnect, Rapid7’s Security Orchestration Automation and Response (SOAR) tool, takes detection and response capabilities to the next level. Joint customers of InsightIDR and InsightConnect are able to:
Auto-enrich alerts
Let machines do the heavy lifting and eliminate the manual effort it takes to enrich indicators in your SIEM alerts. By enriching the quality of the alerts you receive, InsightConnect can automatically filter out false positives and accelerate detection, giving security teams more time to focus on the threats that matter most.
Customize alerting and escalation pathways
We know customers don’t want to respond to every alert the same way, which is why with InsightConnect, you can define different communication and approval chains based on the type or severity of an alert. Need to respond to alerts on the go? You can maintain 24/7 uptime and drive immediate response actions directly from your chat tools like Microsoft Teams or Slack (which is a lifesaver when you’re away from your desk or working remotely).
Security Planning Tip: Whether all of your organization works in the same office or you’re spread all over the place (with the latter being more likely today), your team likely wants a simple way to collaborate quickly and seamlessly. With the right automation, you can take the alerts that come in from your security tools and delegate tasks from back to other connected tools, making communication and case management bi-directional, saving everyone time, and ensuring that nothing slips through the cracks.
Auto-contain threats
Reduce time to containment and stop attackers early by automatically containing threats related to high risk alerts. Security analysts can stop attackers from every angle by integrating InsightConnect across their technology stack to block IP addresses, ban hashes, and quarantine assets before threats can infiltrate their organizations.
These are just a few examples of what InsightConnect can do for you in InsightIDR—check out our guide Optimize Security Operations with Automation to see more use cases.
Get started with InsightIDR and InsightConnect
As the threat landscape continues to evolve in 2021, automation will continue to play a critical role in successful detection and response. Get started with InsightIDR and InsightConnect today to gain more visibility into your environment, drastically reduce alert fatigue, and accelerate response.
We hope these tips are helpful as you ramp up on planning! Check out the other posts in this series for more advice ad ideas to make your security program a success going into the new year:
Article Tags
Related blog posts

Detection and Response
Zero Chaos: Scaling Detection Engineering at the Speed of Software, with Detection As Code
Zachary Zeid, James Gallahan
Threat Research
Rapid7 Detection Coverage for Iran-Linked Cyber Activity
Rapid7 Labs

Detection and Response
Alert Fatigue Isn’t Going Away. Here’s How Modern SOCs Are Fighting Back
Rapid7

Detection and Response
Rapid7: 7 years of recognition in Gartner® Magic Quadrant™ for SIEM
Cindy Stanton
