Posts tagged Malware

Threat Research
When IT Support Calls: Dissecting a ModeloRAT Campaign from Teams to Domain Compromise
Anna Širokova

Threat Research
Kyber Ransomware Double Trouble: Windows and ESXi Attacks Explained
Anna Širokova
Threat Research
The Chrysalis Backdoor: A Deep Dive into Lotus Blossom’s toolkit
Ivan Feigl

Threat Research
Inside Russian Market: Uncovering the Botnet Empire
Alexandra Blia, Maor Weinberger
Threat Research
An Earth-Shattering Kaboom: Bringing a Physical ICS Penetration Testing Environment to Life (Part 2)
Anna Katarina Quinn

Threat Research
An Earth-Shattering Kaboom: Bringing a Physical ICS Penetration Testing Environment to Life (Part 1)
Anna Katarina Quinn

Threat Research
Emerging Trends in AI-Related Cyberthreats in 2025: Impacts on Organizational Cybersecurity
Jeremy Makowski

Threat Research
Filch Stealer: A new infostealer leveraging old techniques
Ivan Feigl

Vulnerabilities and Exploits
BlackSuit Continues Social Engineering Attacks in Wake of Black Basta’s Internal Conflict
Tyler McGraw

Vulnerabilities and Exploits
NSIS Abuse and sRDI Shellcode: Anatomy of the Winos 4.0 Campaign
Anna Širokova, Ivan Feigl
Detection and Response
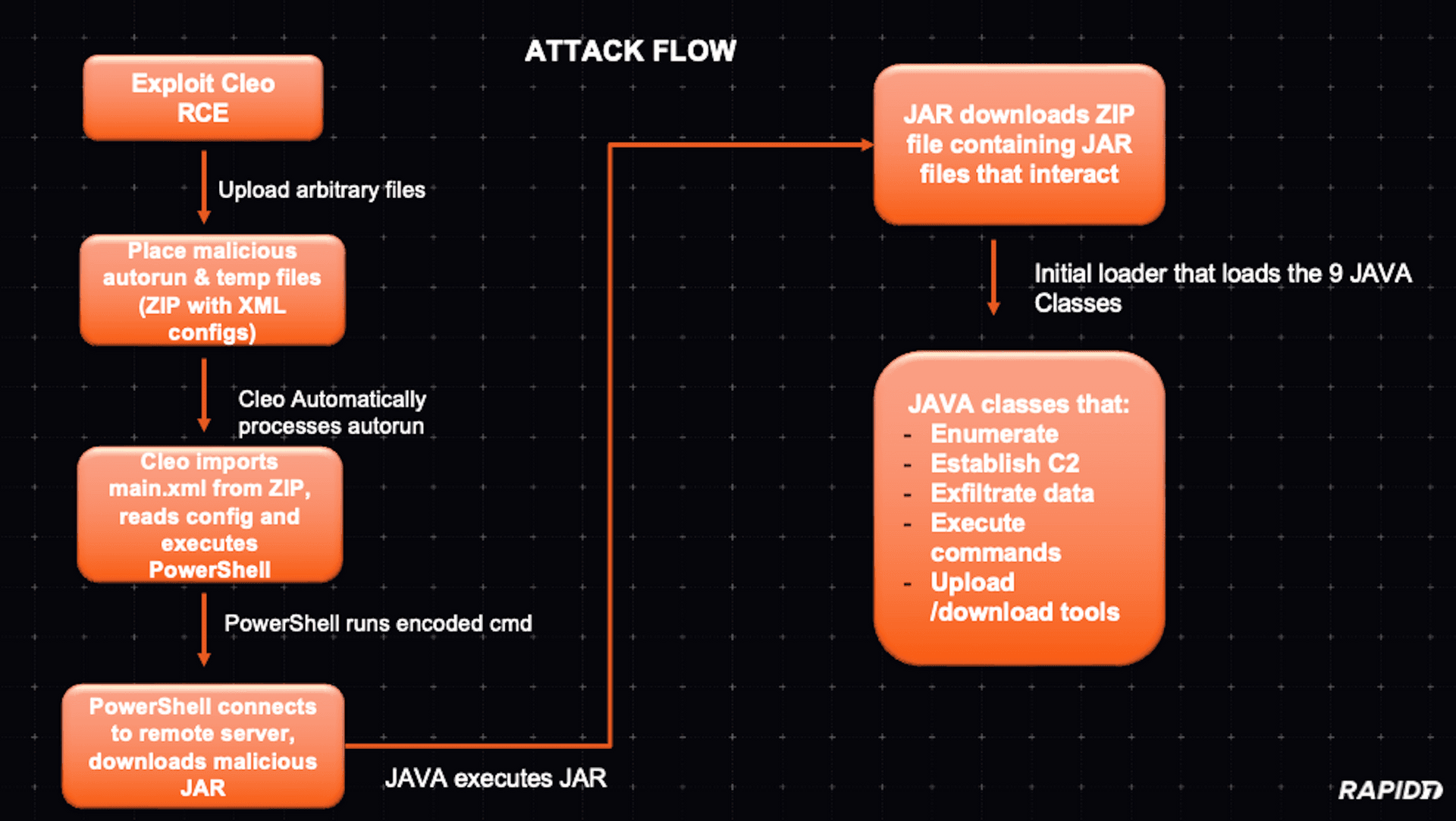
Modular Java Backdoor Dropped in Cleo Exploitation Campaign
Christiaan Beek
Detection and Response
Black Basta Ransomware Campaign Drops Zbot, DarkGate, and Custom Malware
Tyler McGraw
Industry Trends
Why Cybercriminals Are Not Necessarily Embracing AI
Christiaan Beek
Vulnerabilities and Exploits
New “CleverSoar” Installer Targets Chinese and Vietnamese Users
Natalie Zargarov
Threat Research
A Bag of RATs: VenomRAT vs. AsyncRAT
Anna Širokova

Threat Research
LodaRAT: Established Malware, New Victim Patterns
Natalie Zargarov

Vulnerabilities and Exploits
Malware Campaign Lures Users With Fake W2 Form
Tom Elkins
Detection and Response
Ongoing Malvertising Campaign Leads to Ransomware
Tyler McGraw

Detection and Response
Stories from the SOC Part 2: MSIX Installer Utilizes Telegram Bot to Execute IDAT Loader
Tom Elkins

Products and Tools
Stories from the SOC Part 1: IDAT Loader to BruteRatel
Tom Elkins

Vulnerabilities and Exploits
How To Hunt For UEFI Malware Using Velociraptor
Matthew Green