Posts by Adam Cammack

Exposure Management
Metasploit Wrap-Up: 3/12/21
Adam Cammack

Exposure Management
Metasploit Wrap-Up: 11/20/20
Adam Cammack

Products and Tools
Metasploit Wrap-Up: 7/24/20
Adam Cammack

Exposure Management
Metasploit Wrap-Up 4/24/20
Adam Cammack

Exposure Management
Memory Laundering: Is Cleaner Better?
Adam Cammack

Exposure Management
Metasploit Wrap-Up: 11/22/19
Adam Cammack

Products and Tools
Metasploit Wrap-Up 8/30/19
Adam Cammack

Products and Tools
Metasploit Wrap-Up 8/23/19
Adam Cammack
Products and Tools
Metasploit Wrap-Up 5/24/19
Adam Cammack

Products and Tools
Metasploit Wrap-Up 2/22/19
Adam Cammack

Exposure Management
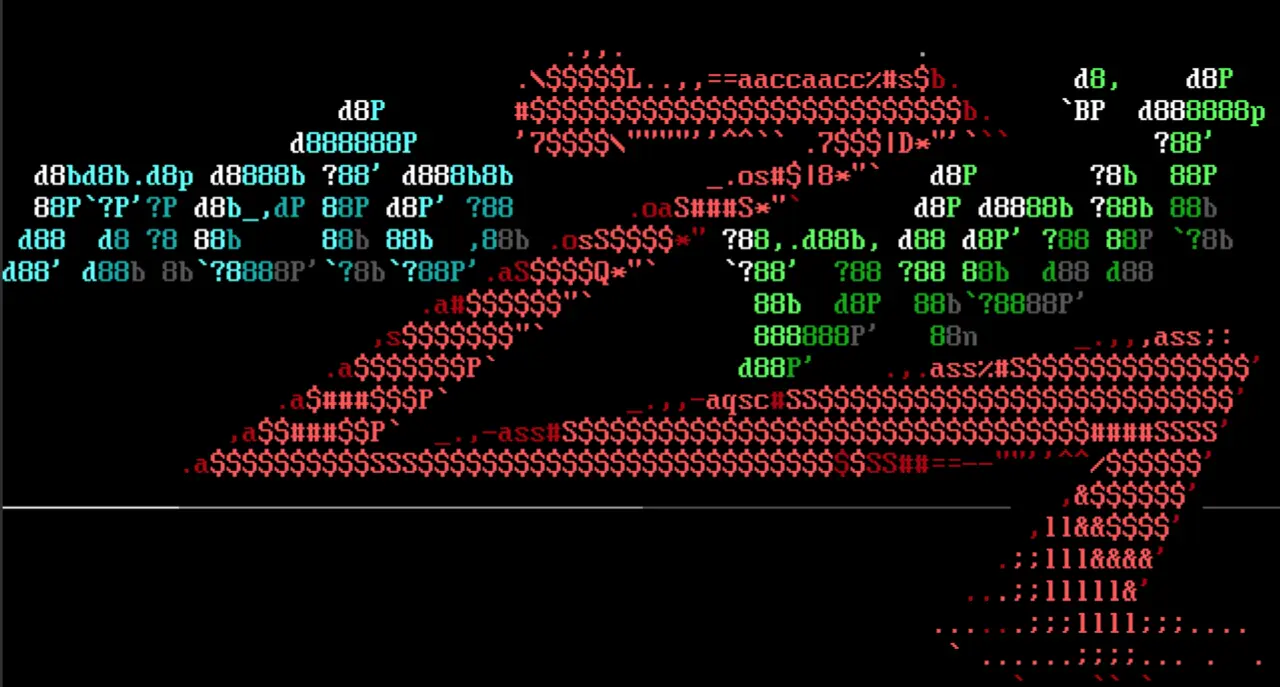
Santa's ELFs: Running Linux Executables Without execve
Adam Cammack
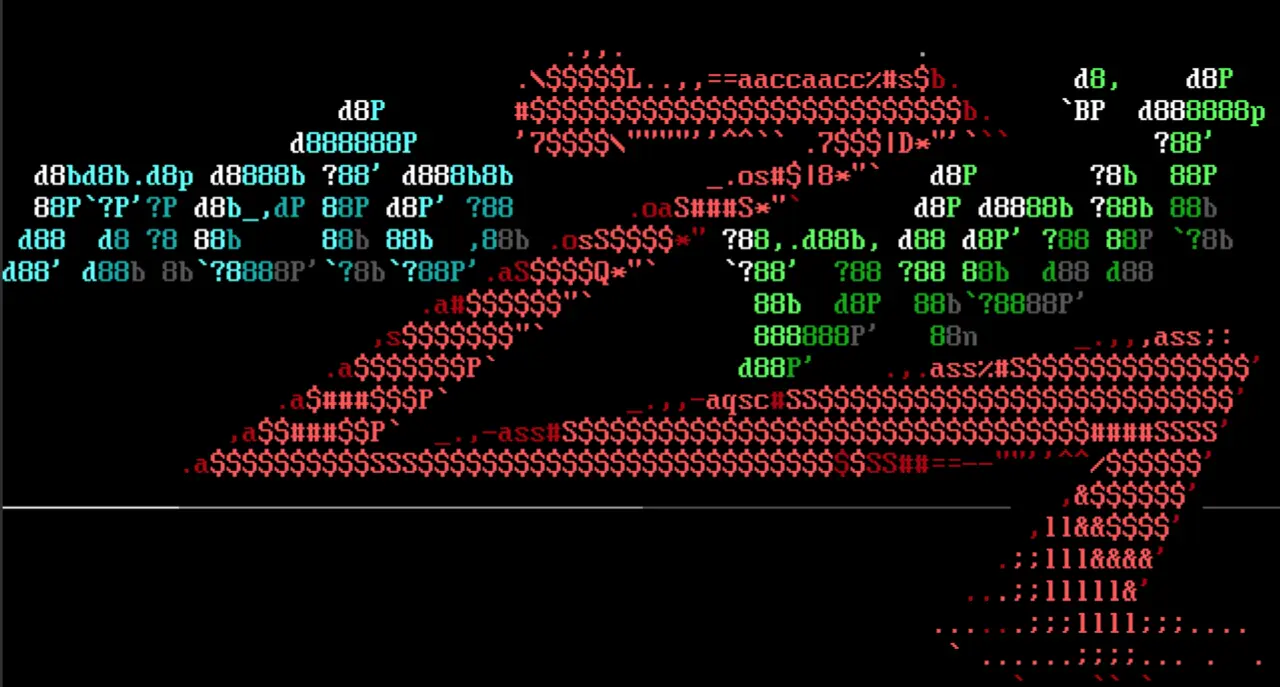
Products and Tools
Metasploit Wrapup 11/30/18
Adam Cammack

Products and Tools
Metasploit Wrapup 9/7/18
Adam Cammack

Products and Tools
External Metasploit Modules: The Gift that Keeps on Slithering
Adam Cammack

Products and Tools
Metasploit Wrapup 6/8/18
Adam Cammack

Products and Tools
Regifting Python in Metasploit
Adam Cammack