Crock-Pot cooking with Metasploit
Belkin's Wemo line of smart home devices offers users a variety of internet-connected gadgets and gizmos they can control around the home. One of those happens to be a Crock-Pot. We went ahead and bought one.
Naturally, it made sense for us to write a module to control our new slow cooker via the UPnP actions it exposed. Check it out!
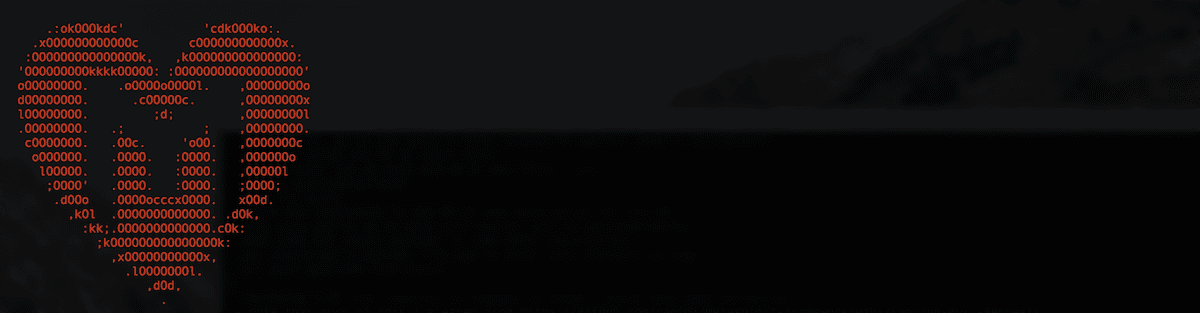
msf5 > use auxiliary/admin/wemo/crockpot
msf5 auxiliary(admin/wemo/crockpot) > set rhosts 10.22.22.1
rhosts => 10.22.22.1
msf5 auxiliary(admin/wemo/crockpot) > set temp High
temp => High
msf5 auxiliary(admin/wemo/crockpot) > set time 1
time => 1
msf5 auxiliary(admin/wemo/crockpot) > set defangedmode false
defangedmode => false
msf5 auxiliary(admin/wemo/crockpot) > set verbose true
verbose => true
msf5 auxiliary(admin/wemo/crockpot) > run
[+] Wemo-enabled Crock-Pot detected
[*] Cooking on High for 1m
[+] Cook time set to 1m
[*] Auxiliary module execution completed
msf5 auxiliary(admin/wemo/crockpot) >
It's important to note that the module implements a subset of the functionality already provided by the Wemo App, and no vulnerabilities are exploited in any way — but now you can cook with Crock-Pot in new and interesting network scenarios.
Bon appétit and bring on the queso!
PowerShell history for the taking
Everyone knows the best way to get to know someone is to read their shell history. Thanks to a convenient tweet by Nikhil Mittal, contributor Garvit Dewan has added a post module to gather PSReadline history. You might be surprised what you'll find.
Enhanced John the Ripper support
Thanks to the indomitable h00die's diligent work in PRs #11335 and #11351, John the Ripper support in Metasploit has never been better. Next time you go to crack hashes in Metasploit, give h00die some praise for doing a thankless job!
New Modules
Exploit modules (2 new)
- Adobe Flash Player DeleteRangeTimelineOperation Type-Confusion by Genwei Jiang and bcook-r7, which exploits CVE-2016-4117
- Microsoft Excel .SLK Payload Delivery by Carter Brainerd, Pieter Ceelen, and Stan Hegt
Auxiliary and post modules (9 new)
- Unitronics PCOM remote START/STOP/RESET command by Luis Rosa
- Belkin Wemo-Enabled Crock-Pot Remote Control by wvu
- Crack Hashes in the Database Using John the Ripper .pot Files by h00die
- JVC/Siemens/Vanderbilt IP-Camera Readfile Password Disclosure by Yakir Wizman and h00die
- SAP Management Console List Config Files by Chris John Riley and Jacobo Avariento Gimeno
- Unitronics PCOM Client by Luis Rosa
- Solaris pfexec Upgrade Shell by bcoles
- Windows Gather PSReadline History by Garvit Dewan
Improvements
- #11239 improves the check method for docker_daemon_privilege_escalation to be able to check for writable and nosuid WritableDir.
- #11335 adds or fixes jtr_format in hash-dumping modules.
- #11351 modernizes Metasploit's interaction with the John the Ripper password cracker.
- #11371 adds documentation to auxiliary/scanner/http/rips_traversal.
- #11384 adds documentation to auxiliary/scanner/http/dir_listing.
- #11394 adds documentation to auxiliary/gather/cisco_rv320_config.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate and you can get more details on the changes since the last blog post from GitHub:
We recently-announced the release of Metasploit 5. You can get it by cloning the Metasploit Framework repo (master branch). To install fresh without using git, you can use the open-source-only Nightly Installers or the binary installers (which also include the commercial editions). PLEASE NOTE that the binary installers, and Metasploit Framework versions included in distros such as Kali, Parrot, etc., are based off the Metasploit 4 branch for the time being. Migration is underway, so you can look forward to getting Metasploit 5 in the binary installers and in third-party software distributions soon.