Posts by William Vu

Exposure Management
Metasploit Wrap-Up: 6/12/20
William Vu

Products and Tools
Metasploit Wrap-Up: 2/21/20
William Vu
Products and Tools
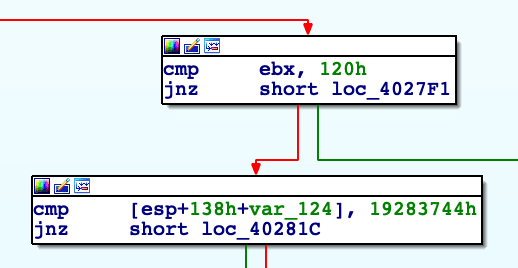
DOUBLEPULSAR RCE 2: An RDP Story
William Vu

Products and Tools
Metasploit Wrap-Up 11/15/19
William Vu
Products and Tools
Open-Source Command and Control of the DOUBLEPULSAR Implant
William Vu
Products and Tools
Metasploit Wrap-Up 8/16/19
William Vu
Products and Tools
Metasploit Wrap-Up 2/15/19
William Vu

Threat Research
The Ghost of Exploits Past: A Deep Dive into the Morris Worm
William Vu

Products and Tools
Metasploit Wrapup: 7/13/18
William Vu

Products and Tools
Weekly Metasploit Wrapup: March 14, 2016
William Vu

Products and Tools
New "show missing" Command in msfconsole
William Vu

Products and Tools
Making Your Printer Say "Feed Me a Kitten" and Also Exfiltrate Sensitive Data
William Vu