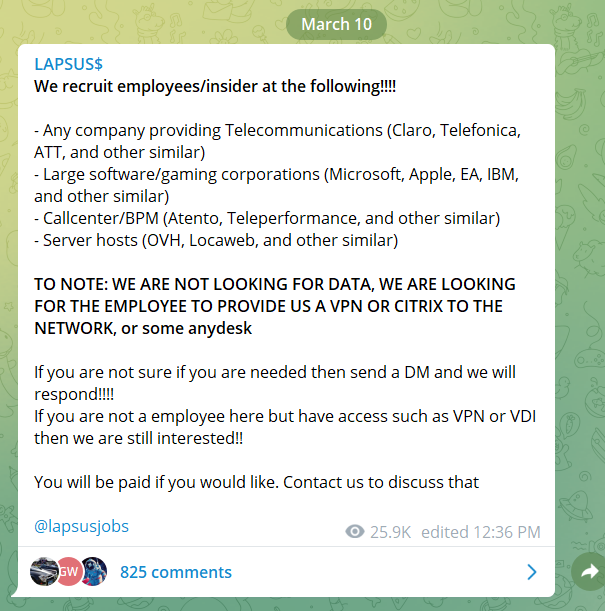
The Lapsus$ ransomware gang’s modus operandi seems to be evolving. Following the recent data breaches of Nvidia and Samsung, on March 10, 2022, the Lapsus$ ransomware gang posted a message on their Telegram channel claiming that they were looking to recruit employees/insiders of companies in the telecommunications, software/gaming, call center/BPM, and server hosting industries.
This marks a departure from their previous attacks, which relied on phishing to gain access to victims’ networks. Now they are taking a more direct approach, actively recruiting employees who can provide them with VPN or Citrix access to corporate networks.
Additionally, the group appears to be taking requests. On March 6, 2022, Lapsus$ posted a survey on their Telegram channel asking people which victim’s source code they should leak next.
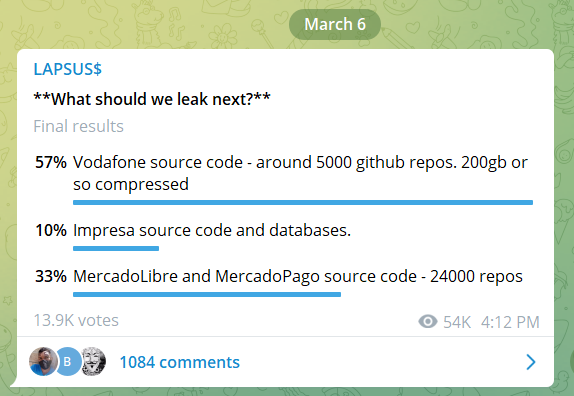
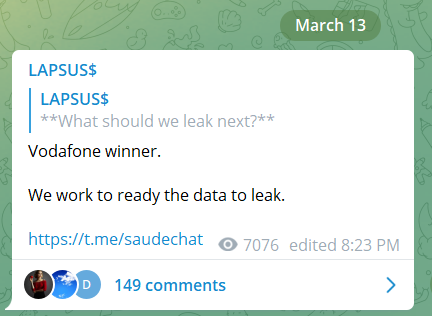
Following this survey, on March 12, 2022, the Lapsus$ ransomware gang posted a message on its Telegram channel in which they claimed to have hacked the source code of Vodafone Group. The next day, March 13, they posted another message to say that they are preparing the Vodafone data to leak.
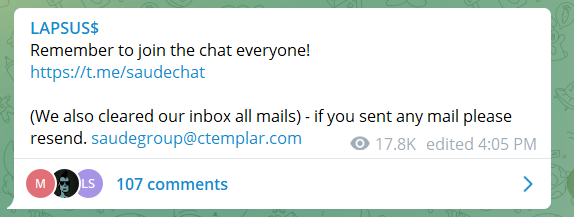
The Lapsus$ ransomware gang calls on people to join their Telegram chat group or contact them by email at the following address: [email protected].
Generally, cybercriminal groups exploiting ransomware infect employee computers by using techniques such as phishing or Remote Access Trojans. However, the Lapsus$ ransomware gang’s bold new approach to target companies from within is concerning and shows their willingness to expand their capabilities and attack vectors.
As a result, we recommend that companies increase the vigilance they exercise regarding their internal security policy. Regardless of whether Lapsus$ recruiting tactics prove successful, they emphasize the need for proper user access control. It is critical to ensure that employees with access to the company network have only the security rights they require and not more.
To learn more about Rapid7’s role-based access control capabilities, check out Solving the Access Goldilocks Problem: RBAC for InsightAppSec Is Here.
Additional reading:
- Conti Ransomware Group Internal Chats Leaked Over Russia-Ukraine Conflict
- Russia-Ukraine Cybersecurity Updates
- The Top 5 Russian Cyber Threat Actors to Watch
- For Health Insurance Companies, Web Apps Can Be an Open Wound
Related blog posts

Threat Research
Muddying the Tracks: The State-Sponsored Shadow Behind Chaos Ransomware
Alexandra Blia, Ivan Feigl

Industry Trends
Experts on Experts: The 2026 Threat Landscape is Moving Faster than Defenders Expect
Craig Adams

Threat Research
New Whitepaper: Stealthy BPFDoor Variants are a Needle That Looks Like Hay
Rapid7 Labs

Threat Research
BPFdoor in Telecom Networks: Sleeper Cells in the Backbone
Rapid7 Labs
