Posts tagged Third-Party Disclosure

Vulnerabilities and Exploits
R7-2019-39 | CVE-2019-5648: LDAP Credential Exposure in Barracuda Load Balancer ADC (FIXED)
Sam Huckins

Vulnerabilities and Exploits
R7-2019-09 | CVE-2019-5617, CVE-2019-5643, CVE-2019-5644: C4G BLIS authentication and authorization vulnerabilities (FIXED)
Sam Huckins

Detection and Response
Investigating the Plumbing of the IoT Ecosystem (R7-2018-65, R7-2019-07) (FIXED)
Tod Beardsley

Vulnerabilities and Exploits
R7-2019-01: CircuitWerkes Sicon-8 Client-Side Authentication Read-Only Bypass (CVE-2019-5616)
Tod Beardsley

Vulnerabilities and Exploits
R7-2018-52: Guardzilla IoT Video Camera Hard-Coded Credential (CVE-2018-5560)
Tod Beardsley
Vulnerabilities and Exploits
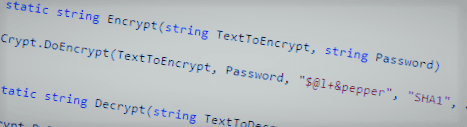
R7-2018-01 (CVE-2018-5551, CVE-2018-5552): DocuTrac Office Therapy Installer Hard-Coded Credentials and Cryptographic Salt
Tod Beardsley

Vulnerabilities and Exploits
R7-2017-25: Cambium ePMP and cnPilot Multiple Vulnerabilities
Tod Beardsley

Vulnerabilities and Exploits
R7-2017-08: BPC SmartVista SQL Injection Vulnerability
Sam Huckins

Vulnerabilities and Exploits
Multiple vulnerabilities in Wink and Insteon smart home systems
Sam Huckins

Vulnerabilities and Exploits
R7-2017-07: Multiple Fuze TPN Handset Portal vulnerabilities (FIXED)
Sam Huckins

Vulnerabilities and Exploits
R7-2017-06 | CVE-2017-5241: Biscom SFT XSS (FIXED)
Tod Beardsley

Vulnerabilities and Exploits
R7-2017-05 | CVE-2017-3211: Centire Yopify Information Disclosure
Sam Huckins

Vulnerabilities and Exploits
R7-2016-23, R7-2016-26, R7-2016-27: Multiple Home Security Vulnerabilities
Tod Beardsley

Vulnerabilities and Exploits
R7-2016-28: Multiple Eview EV-07S GPS Tracker Vulnerabilities
Tod Beardsley

Vulnerabilities and Exploits
R7-2017-01: Multiple Vulnerabilities in Double Robotics Telepresence Robot
Sam Huckins

Vulnerabilities and Exploits
R7-2016-24, OpenNMS Stored XSS via SNMP (CVE-2016-6555, CVE-2016-6556)
Tod Beardsley

Vulnerabilities and Exploits
R7-2016-07: Multiple Vulnerabilities in Animas OneTouch Ping Insulin Pump
Tod Beardsley

Vulnerabilities and Exploits
Multiple Disclosures for Multiple Network Management Systems, Part 2
Tod Beardsley

Vulnerabilities and Exploits
R7-2016-08: Seeking Alpha Mobile App Unencrypted Sensitive Information Disclosure
Tod Beardsley

Vulnerabilities and Exploits
R7-2016-06: Remote Code Execution via Swagger Parameter Injection (CVE-2016-5641)
Scott Davis

Vulnerabilities and Exploits
R7-2016-02: Multiple Vulnerabilities in ManageEngine OpUtils
Tod Beardsley