As we turn the corner into the new year, our team has been looking back at 2019 and reflecting on some of our most exciting updates and additions. Going into the year, our mission was to help security teams find the efficiencies they need to tackle mounting complexity and build successful threat detection and response programs. We are thrilled with the feedback that we’ve received from customers so far, and confident in the road ahead and our ability to advance security for all. This post is a rundown of highlights from InsightIDR, Rapid7's SIEM solution, in 2019.
Address compliance needs with file integrity monitoring
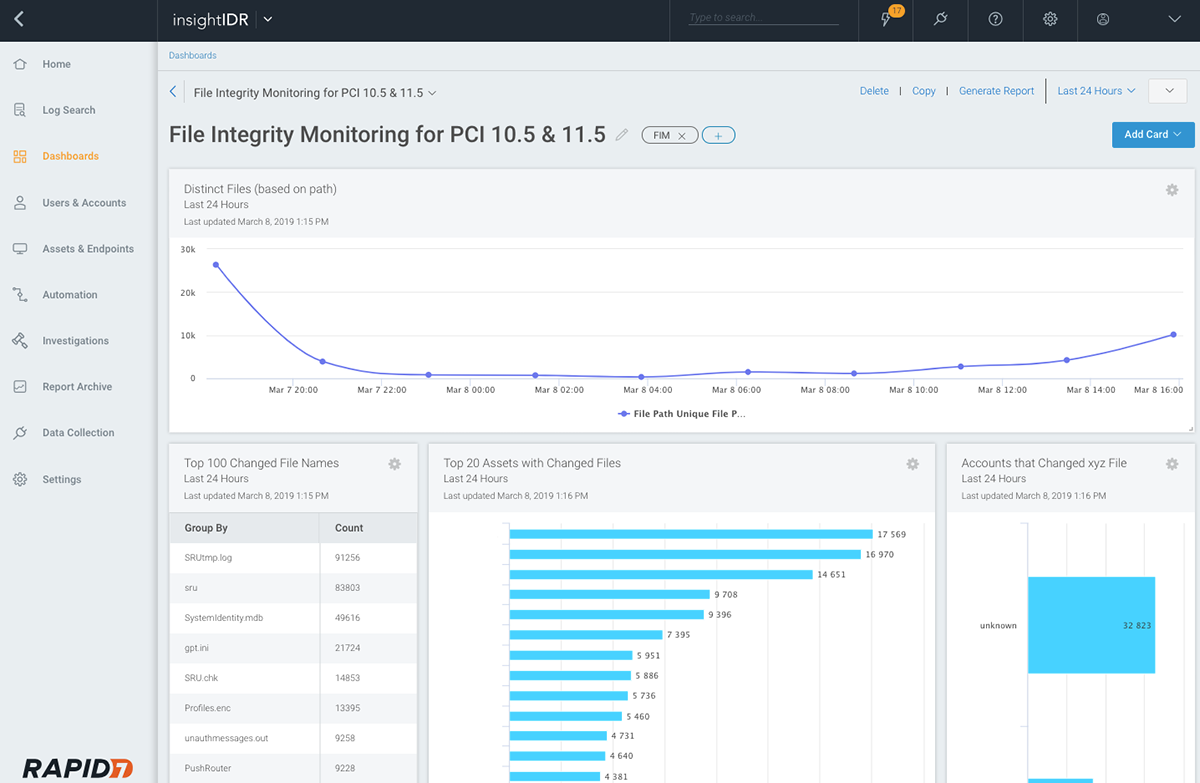
This year brought the introduction of file integrity monitoring (FIM) in InsightIDR. FIM is a great tool to be able to ensure sensitive files aren’t tampered with or accessed by potentially malicious actors. It is also a core component of a number of compliance regulations. With the Insight Agent deployed to critical assets, InsightIDR customers can easily activate FIM to flag changes to specified files or directories on that endpoint.
Stay ahead of attackers in the cloud
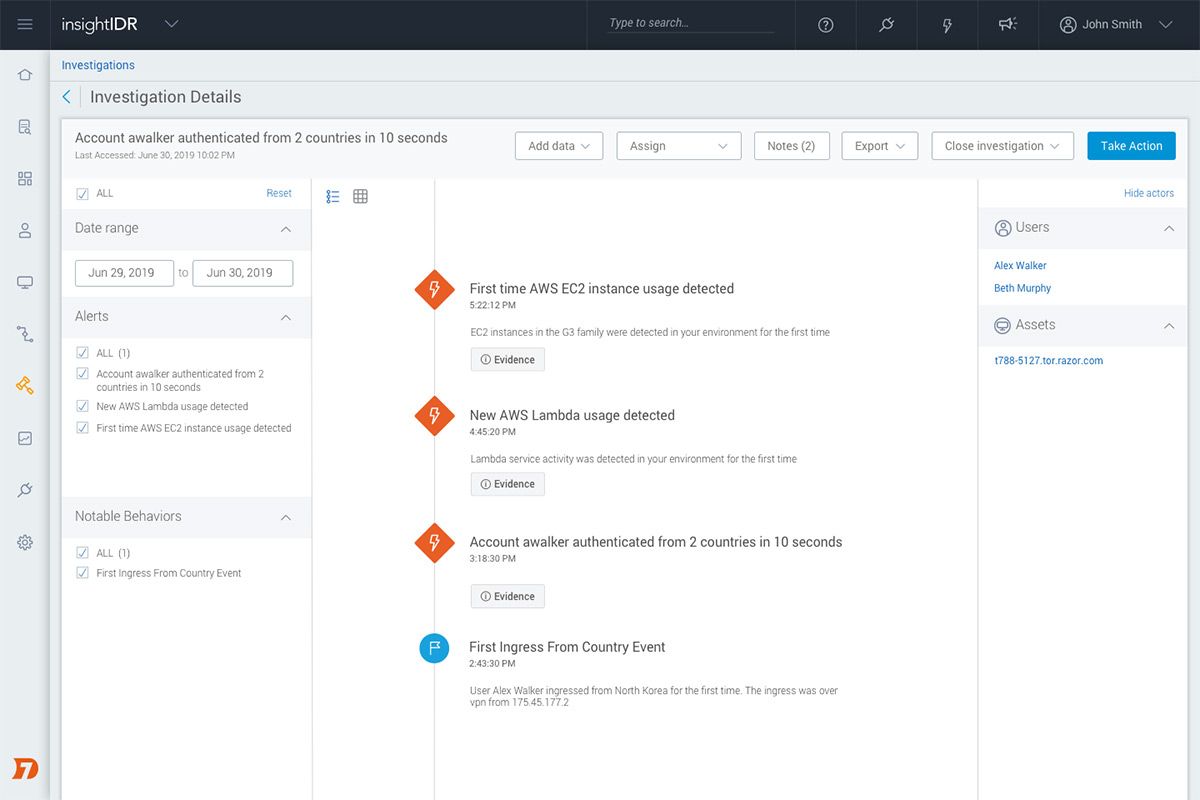
As organizations increasingly adopt cloud infrastructure and applications, we know security teams are challenged to keep pace with an ever-evolving technology footprint and their accelerated DevOps counterparts. Many of our customers are now working in hybrid and multi-cloud environments, and they are dealing with new types of data and threats as a result. To give teams visibility and reliable detections in these infrastructures, we’ve upped our support for AWS and Azure environments this year. Customers can monitor these—as well as the other diverse datasets from across their environment—from a consolidated and intuitive interface in InsightIDR.
Learn about potential threats in AWS and InsightIDR’s pre-built detections here.
Easily structure and act on data
As security teams work with sprawling (and often unique) data sets, analysts need an easy way to find the information they need quickly and take action. The Parsing Tool in InsightIDR is an intuitive, wizard-style experience that helps analysts create key-value pairs (a la JSON) from custom or support event sources. With data structured and tailored to pull out the information that analysts care about most, teams can easily search, visualize, and create alerts from these data sets.
Accelerate investigations with automation
Automation is increasingly becoming a prerequisite for security teams to be successful in increasingly complex environments and threat landscapes. InsightIDR has been investing in automation capabilities and increased synergy with Rapid7’s SOAR product, InsightConnect, for several years now. In 2019, we continued these investments to help our customers build momentum and get started with automation. One of our more recent additions in this area is the ability for customers to automatically enrich alerts with open source threat intelligence. This additional information can provide helpful context for investigations and help expedite the overall response process.
To learn more about alert enrichment workflows in InsightIDR, check out our blog post here.
Track progress and trends with Security Operations Activity Dashboard
One recent release we were very excited about was the launch of our Security Operations Activity Dashboard. With this snapshot, InsightIDR customers can easily get an executive summary of their organization’s threat landscape and analyst response trends. This includes real-time visibility for things like investigation activity, alert and attack chain trends, and analyst and team progress. This dashboard can help teams track performance over time and is also a resource that can be easily shared with leadership and business stakeholders to summarize security operations and activity.
More to come!
Again, these are just a few of the highlights from a great year with InsightIDR. Thank you to all of our customers for your continued partnership in helping drive our products forward. In the year ahead, we look forward to working with you and continuing to help teams tackle complexity and further their threat detection and response programs.
Related blog posts

Detection and Response
Zero Chaos: Scaling Detection Engineering at the Speed of Software, with Detection As Code
Zachary Zeid, James Gallahan
Threat Research
Rapid7 Detection Coverage for Iran-Linked Cyber Activity
Rapid7 Labs

Detection and Response
Alert Fatigue Isn’t Going Away. Here’s How Modern SOCs Are Fighting Back
Rapid7

Detection and Response
Rapid7: 7 years of recognition in Gartner® Magic Quadrant™ for SIEM
Cindy Stanton